Microsoft released the Agent Governance Toolkit on April 3, 2026, the first open-source framework to address all 10 OWASP agentic AI risks with deterministic, sub-millisecond policy enforcement. The timing isn’t coincidental. Autonomous AI agents are moving to production, EU AI Act obligations take effect August 2, and Colorado’s AI Act becomes enforceable June 30. Runtime governance just shifted from “nice to have” to “regulatory requirement.”
Why Agentic AI Security Is Different
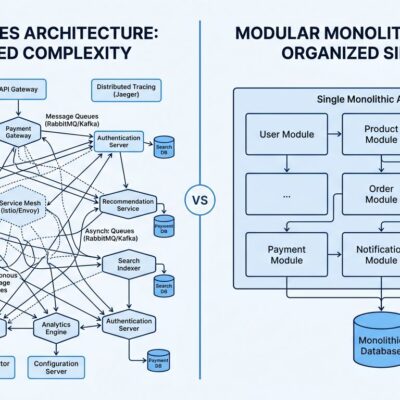
Traditional AI security focuses on the model layer: prompt injection, data leakage, hallucination. Agentic AI security extends to the action layer—the tools agents invoke, the credentials they hold, the systems they modify, and the multi-agent workflows they participate in. This is the distinction that matters.
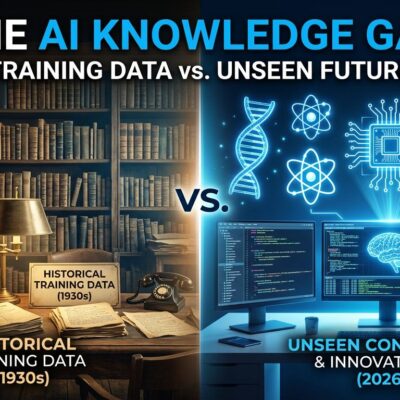
In December 2025, OWASP published the Top 10 for Agentic Applications, the first formal taxonomy of risks specific to autonomous AI agents. These aren’t theoretical: goal hijacking occurs when attackers manipulate agent objectives through poisoned inputs like emails or documents. Tool misuse happens when agents use legitimate tools in unsafe ways—calling destructive parameters or chaining tools into data exfiltration sequences. Memory poisoning corrupts an agent’s long-term context so future reasoning is skewed. Rogue agents drift from intended behavior and act with harmful autonomy.
A Dark Reading poll found that 48% of cybersecurity professionals identify agentic AI as the number-one attack vector for 2026, outranking deepfakes, ransomware, and supply chain attacks. The threat model changed. The security tools didn’t catch up—until now.
What the Toolkit Does
The Agent Governance Toolkit sits between your agent framework and the actions agents take. Every tool call, resource access, and inter-agent message gets evaluated against policy before execution. The policy engine runs in sub-millisecond latency—p99 below 0.1 milliseconds—so governance doesn’t slow production systems.
The toolkit ships as seven independently installable packages: Agent OS (core policy engine), Agent Mesh (cryptographic identity and inter-agent trust protocol), Agent Runtime (execution sandboxing with privilege rings), Agent SRE (circuit breakers and error budgets for production reliability), Agent Compliance (automated EU AI Act and HIPAA mapping), Agent Marketplace (signed plugin verification), and Agent Lightning (reinforcement learning governance). Each package targets a specific layer of the agentic security stack.
Here’s how it addresses OWASP risks in practice: semantic intent classifiers detect goal hijacking attempts. Capability sandboxing prevents tool misuse. Decentralized identifiers with Ed25519 signing stop identity abuse. Plugin signing with manifest verification secures the supply chain. Execution rings with resource limits contain unexpected code execution. Cross-model verification with majority voting catches memory poisoning. The Inter-Agent Trust Protocol encrypts communications. Circuit breakers prevent cascading failures. Approval workflows with quorum logic block human-agent trust exploitation. Ring isolation, trust decay, and automated kill switches handle rogue agents.
Microsoft published the toolkit under MIT license and designed it framework-agnostic. It works with LangChain, CrewAI, OpenAI Agents, Google ADK, AWS Bedrock, Azure AI, and 20+ other platforms. Install with pip, npm, or NuGet. The project ships with 9,500+ tests.
Regulatory Deadlines Are Real
The EU AI Act’s high-risk AI obligations take effect August 2, 2026—62 days from today. Colorado’s AI Act becomes enforceable June 30—61 days. Both require risk management policies, impact assessments, monitoring and logging systems, and human oversight controls for high-risk AI applications. Colorado’s law is self-executing: the Attorney General can enforce without waiting for rulemaking.
For developers deploying AI agents in employment, housing, credit, healthcare, insurance, education, or legal services, you have 60 days to implement governance or face legal liability. Colorado’s penalties run up to $20,000 per violation. The law includes an affirmative defense: compliance with a recognized risk management framework—like the Agent Governance Toolkit—provides legal protection.
This isn’t distant future regulation. The clock is running.
The Threat Isn’t Hypothetical
OpenClaw, the viral open-source AI agent with 135,000 GitHub stars, triggered the first major agentic security crisis of 2026 with multiple critical vulnerabilities and over 21,000 exposed instances. Between December 2025 and January 2026, an attacker used Claude to breach multiple Mexican government agencies, stealing 150GB of data including 195 million taxpayer records. The attacker’s conversation logs were found publicly accessible online. Arup, the international engineering firm, lost $25 million in September 2026 to a deepfake fraud scheme exploiting human-agent trust.
These aren’t edge cases. A 2026 survey found that 88% of enterprises experienced AI agent security incidents. The pattern is clear: agents granted excessive access without runtime governance create exploitable attack surfaces. The XZ Utils backdoor in March 2024 demonstrated how attackers use social engineering on burned-out maintainers. Agentic systems facing goal hijacking and tool misuse attacks don’t need social engineering—the attack vector is the input data itself.
What Developers Should Do
The Agent Governance Toolkit is open source, production-ready, and framework-agnostic. If you’re deploying autonomous AI agents—especially in regulated industries or high-risk applications—you need runtime governance before regulations enforce it. The alternative is building your own security layer or waiting for an incident to force the issue.
Microsoft’s release doesn’t solve every agentic security problem, but it’s the first comprehensive framework that addresses the OWASP taxonomy systematically. The sub-millisecond performance and MIT licensing remove the two biggest friction points: operational overhead and cost. Install it, configure policies for your risk tolerance, and deploy.
Regulatory compliance starts August 2. Security incidents are already happening. The toolkit is available now. The gap between “should adopt” and “must adopt” closes in 60 days.