A critical Linux kernel vulnerability disclosed April 29, 2026, allows any unprivileged user to gain root access on every major Linux distribution using a 732-byte Python script. CVE-2026-31431, dubbed “Copy Fail,” has affected Ubuntu, RHEL, Amazon Linux, SUSE, and other distributions since 2017—a nine-year window exposing millions of servers worldwide. Moreover, the exploit was discovered by Theori’s AI-powered Xint Code platform in approximately one hour, demonstrating how artificial intelligence is fundamentally changing vulnerability research economics.
The CVE-2026-31431 Exploit: 732 Bytes to Root
Copy Fail exploits a logic bug in the Linux kernel’s algif_aead cryptographic template to perform a deterministic 4-byte write to the page cache of any readable file. Furthermore, the attack combines three kernel components: AF_ALG sockets that expose crypto operations to unprivileged users, the splice() system call that delivers file pages to crypto sockets, and the authencesn algorithm that writes beyond its output buffer directly into memory.
The result is remarkably simple. This 732-byte Python script modifies setuid binaries like /usr/bin/su in memory, injecting shellcode that executes with root privileges. No race conditions, no distribution-specific tuning, no guesswork required. Consequently, it works 100% reliably across Ubuntu 24.04 LTS, Amazon Linux 2023, RHEL 14.3, SUSE 16, and virtually every Linux distribution shipped since 2017.
# Simplified attack flow (pseudocode)
alg_socket = socket(AF_ALG, SOCK_SEQPACKET, 0)
alg_socket.bind(("aead", "authencesn(hmac(sha256),cbc(aes))"))
# Splice target file into crypto socket
splice(target_file_fd, crypto_socket_fd, offset)
# Trigger AEAD operation → writes to page cache
recv(alg_socket) # Corrupts /usr/bin/su in memory
# Execute corrupted binary
execve("/usr/bin/su") # Root shellThe simplicity contrasts sharply with the devastation. Security researcher David Brumley noted this type of vulnerability “tends to sell on the broker market for the price of a house”—historically valued at over $500,000. Nevertheless, AI tools found it faster than a coffee break.
Nine Years Hidden in Plain Sight
The vulnerability was introduced in 2017 when kernel developers optimized AEAD cryptographic operations to run “in-place,” merging source and destination memory buffers for performance. For nine years, the bug went undetected in the world’s most-reviewed codebase. Additionally, the flaw stemmed from a dangerous assumption: the kernel’s crypto API assumed all AEAD algorithms would confine writes to intended destinations, but nothing in the API enforced this guarantee.
Theori researcher Taeyang Lee identified the core issue: “The design assumes every AEAD algorithm will confine its writes to the intended destination, but nothing in the API enforces this.” The authencesn algorithm, used for IPsec Extended Sequence Number support, wrote 4 bytes past its output boundary as scratch space. As a result, those bytes landed directly in the page cache of target files.
The coordinated disclosure timeline from Xint Code shows how quickly the kernel community responded once alerted. Reported March 23, patches were proposed within two days and committed to mainline April 1 (commit a664bf3d603d). CVE-2026-31431 was assigned April 22, with public disclosure April 29 after distributions had time to patch. Herbert Xu’s fix reverts the 2017 optimization, separating source and destination scatterlists to prevent page cache corruption.
AI Found It in One Hour
Here’s the uncomfortable truth: while security experts debated whether AI would replace human researchers, AI just found a half-million-dollar zero-day in an hour. Theori’s Xint Code platform analyzed all userspace-reachable kernel crypto code paths and identified Copy Fail faster than most security reviews take to schedule kickoff meetings.
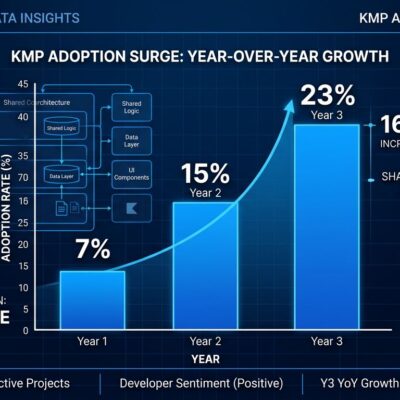
Xint Code’s track record reinforces this isn’t a fluke. With zero human intervention, it found critical RCE bugs in Redis, PostgreSQL, and MariaDB. In fact, it swept the database category at ZeroDay Cloud competition, beating every human team. The platform launched commercially in March 2026, analyzing millions of lines of code in under 12 hours. What took weeks or months of expert analysis now happens while you’re in your morning standup.
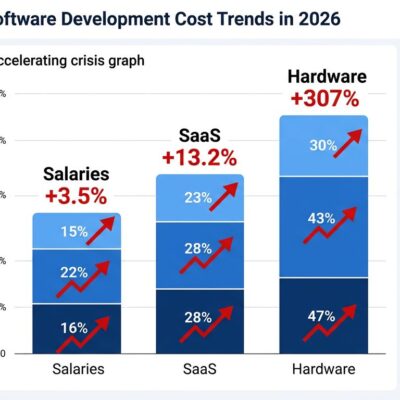
Bugcrowd’s analysis cuts to the core implication: “The cost of finding deep logic flaws may have dropped by something like an order of magnitude through AI-assisted tooling.” If defenders have these tools, assume attackers do too. Therefore, the supply of kernel bugs is no longer constrained by human capacity. Security teams banking on obscurity through complexity are about to have a bad quarter.
Container Escape: Namespace Isolation Isn’t Enough
If you’re treating Docker containers as security boundaries, Copy Fail just invalidated your threat model. The Linux page cache is host-wide, not namespaced. Consequently, a compromised container can exploit Copy Fail to gain root on the node, breaking out of namespace isolation and potentially compromising the entire Kubernetes cluster.
Multi-tenant Kubernetes clusters on shared kernels are particularly exposed. CI/CD runners executing untrusted pull requests become attack vectors. Moreover, AI agent code execution sandboxes running LLM-generated code can escape to the host. Any environment where you’re trusting namespace boundaries for security isolation is vulnerable.
The protected architectures tell the real story. AWS Lambda and Fargate use Firecracker microVMs with hardware virtualization—separate kernels mean Copy Fail can’t bridge the gap. In contrast, Cloudflare Workers run on V8 isolates, not Linux at all. gVisor intercepts syscalls with a user-space kernel, preventing direct kernel access. If your security model depends on the Linux kernel being the boundary, it’s time to reevaluate.
Patch Now: Immediate Action Required
All major distributions have released patches. Ubuntu, RHEL, Amazon Linux, SUSE, Debian—check your package manager. The fix is Herbert Xu’s commit a664bf3d603d, reverting the 2017 in-place optimization. Apply updates and reboot to load the patched kernel. However, for zero-downtime updates, use live kernel patching (kpatch for RHEL, Canonical Livepatch for Ubuntu).
Systems awaiting patches can implement temporary mitigation by disabling the algif_aead kernel module:
# Temporary fix (no reboot required)
echo "install algif_aead /bin/false" > /etc/modprobe.d/disable-algif-aead.conf
rmmod algif_aeadPrioritize multi-tenant environments, CI/CD runners, and internet-facing systems. Every sysadmin managing Linux infrastructure needs to act. Therefore, this isn’t a “patch when convenient” situation—Copy Fail is deterministic, portable, and trivial to exploit.
Key Takeaways
- CVE-2026-31431 enables root access on all major Linux distributions via a 732-byte Python script with 100% reliability—no race conditions or distribution-specific tuning required
- The nine-year vulnerability window (2017-2026) exposes fundamental limits in human code review; AI tools discovered it in one hour, dropping vulnerability research costs by 100x
- Container namespace isolation is insufficient for multi-tenant security—Copy Fail enables container escape via shared page cache; migrate to VM-based isolation (Firecracker, gVisor) for strong guarantees
- Patches are available NOW from all major distributions (commit a664bf3d603d); apply updates and reboot, or use live patching for zero downtime
- Assume attackers have access to similar AI vulnerability discovery tools; accelerate patching cadences and shift to proactive security scanning rather than reactive response
The kernel community responded quickly once alerted, but Copy Fail raises uncomfortable questions about code review effectiveness and the changing economics of vulnerability research. Patch your systems. Reevaluate your container security assumptions. Furthermore, recognize that AI just rewrote the rules of security research—the adversaries already have.