On April 20, 2026, ADT—the company millions trust to protect their homes—got digitally burglarized for the third time in under a year. ShinyHunters, a notorious data extortion group, stole 5.5 million customer records after a voice phishing attack compromised an employee’s Okta SSO account, granting access to ADT’s Salesforce CRM. When ADT refused to pay the ransom by the April 27 deadline, ShinyHunters leaked an 11GB data archive to the dark web. The irony is sharp: a security company that sells protection failed at basic data security. Again.
The Attack Chain: How Vishing Defeated Technical Controls
The breach followed a now-familiar pattern for ShinyHunters: voice phishing (vishing) targeted an ADT employee, compromising their Okta single sign-on credentials. With SSO access, attackers walked straight into ADT’s Salesforce CRM and exfiltrated customer data on 5.5 million people. The technical controls were strong—Okta SSO with multi-factor authentication, Salesforce’s enterprise security. None of it mattered. Social engineering bypassed everything.
Vishing attacks surged 442% in the second half of 2024 and now account for over 60% of phishing-related incident response engagements, according to Mandiant. Voice phishing has overtaken email phishing as the dominant initial intrusion vector in 2026. AI voice cloning makes it scalable and convincing—attackers need just three seconds of audio to produce a replica that fools most people. The FBI issued formal warnings in 2025, but the attacks keep working.
For tech professionals, the lesson is clear: technical security alone isn’t enough. ADT had enterprise-grade tools, but human vulnerability defeated them. Every organization using SSO—which is nearly all of them—faces this same architectural weakness.
ShinyHunters’ Industrialized Extortion
ShinyHunters operates a “pay or leak” business model that’s proven effective across hundreds of breaches. The group, formed in 2019, has hit AT&T (110 million records stolen in 2024, $370,000 ransom paid), Microsoft’s GitHub account, Cisco, Hallmark, Grubhub, and now ADT. They list victims on a dark web leak site, demand payment within 3-7 days, and publish stolen data when companies refuse.
The group has systematically targeted enterprise SSO accounts since 2025, compromising 300-400 organizations via the same attack chain: vishing → SSO credentials → access to downstream SaaS applications like Salesforce, Microsoft 365, and Slack. ADT’s breach followed this exact playbook. The group detected unauthorized access on April 20, publicly disclosed via SEC filing on April 24 (a relatively fast 4-day turnaround), and ShinyHunters leaked the data after the April 27 deadline passed.
The industrialized nature of the campaign is what makes it dangerous. ShinyHunters isn’t exploiting zero-day vulnerabilities or sophisticated malware. They’re exploiting the weakest link in enterprise security: people answering phone calls.
Third Breach in a Year: Pattern of Systemic Failure
One breach is an incident. Two breaches suggest inadequate security. Three breaches in 12 months reveal systemic failure. ADT suffered data breaches in August 2024, October 2024, and now April 2026. For a company whose entire business model is security—protecting homes and families—this pattern is damning.
Consumer trust research shows 66% of people trust companies less after a data breach, and 25% would stop doing business entirely. For a security company, that bar is even higher. If ADT can’t protect its own data after three attempts, why should customers trust them to protect physical homes?
The technical controls weren’t the problem. Okta and Salesforce are industry-standard platforms used by Fortune 500 companies worldwide. The problem is organizational—inadequate security culture, insufficient vishing awareness training, and a failure to learn from previous breaches. Technology can’t fix culture.
What Was Stolen and What It Means
The compromised data includes names, phone numbers, and mailing addresses for 5.5 million customers (confirmed by Have I Been Pwned, though ShinyHunters claims 10 million). A smaller subset of records included dates of birth and the last four digits of Social Security numbers or Tax IDs. Payment information—credit cards, bank accounts—was not accessed. Home security system credentials and access were not compromised.
This is good news/bad news. Your home security system is still secure, and there’s no immediate financial fraud risk. However, names, addresses, and phone numbers are enough for identity theft, social engineering attacks, and SIM swapping. The partial SSN and DOB exposure significantly increases risk for the affected subset. Customers should check Have I Been Pwned, enable credit monitoring and fraud alerts, and change passwords on any accounts using the same credentials.
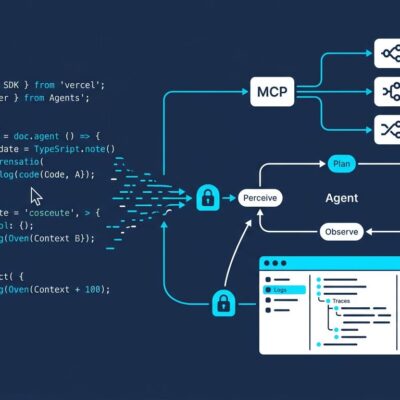
The SSO Single Point of Failure
Single sign-on platforms like Okta exist for good reason—they improve security by centralizing authentication and enabling consistent policy enforcement. But they also create an architectural vulnerability: compromise one SSO account, gain access to every integrated application. For ADT, that meant Salesforce. For other organizations, it could mean Microsoft 365, Slack, GitHub, AWS Console, and dozens of other critical systems.
ShinyHunters understands this architecture and has exploited it across hundreds of organizations. The solution isn’t abandoning SSO—it’s too valuable—but layering additional defenses. Phishing-resistant MFA using FIDO2 hardware keys (not SMS or voice codes) prevents credential theft even during vishing attacks. Callback verification protocols break the attacker’s control over the communication channel—if someone calls requesting credentials, hang up and call back using an official company number. Context-aware access policies can detect anomalous login patterns (unusual locations, times, devices) and require re-authentication. Real-time SSO session monitoring can alert security teams to suspicious activity.
Technical controls are necessary, but process controls—like mandatory callback verification—are what stop vishing attacks. ADT had the technology. They lacked the human-centered defenses that matter most in 2026.
Key Takeaways
- Voice phishing is the dominant enterprise threat vector in 2026, with attacks surging 442% and accounting for over 60% of phishing incidents. Technical controls like MFA can be bypassed through social engineering.
- SSO platforms are a single point of failure. One compromised account grants access to every integrated application. Layer defenses: FIDO2 hardware keys, callback verification protocols, context-aware access policies, and real-time session monitoring.
- Three data breaches in 12 months isn’t bad luck—it’s systemic failure. For security companies especially, repeat breaches damage trust permanently and suggest organizational culture problems that technology alone can’t fix.
- ShinyHunters has industrialized the SSO → SaaS attack chain, compromising 300-400 organizations via vishing since 2025. The attack pattern is reproducible and works across industries.
- If you’re an ADT customer affected by this breach, check Have I Been Pwned for confirmation, enable credit monitoring and fraud alerts, and change passwords on critical accounts. Your home security system itself was not compromised.