Cloudflare announced on April 30, 2026 that AI agents can now autonomously create accounts, purchase domains, start paid subscriptions, and deploy applications—all without human intervention after an initial Terms of Service acceptance. The capability, revealed during “Agents Week 2026,” stems from a new protocol co-designed with Stripe and launched as “Stripe Projects” in open beta. This isn’t agents using your credentials anymore. They’re paying customers with their own accounts.
The shift matters because payment authorization was the missing piece. Agents could call APIs, write code, and execute tasks, but they couldn’t PAY for services. That limitation just evaporated. We now have autonomous software entities provisioning infrastructure and running up bills while you sleep.
How Cloudflare Agents Work: Discovery, Authorization, Payment
The Cloudflare-Stripe protocol operates across three components. First, discovery: agents query the stripe projects catalog command and receive a JSON response listing available services—Cloudflare hosting, domain registration, databases, authentication providers, observability tools. The agent doesn’t need pre-configured service knowledge. Moreover, it discovers options at runtime.
Second, authorization through identity attestation. When a new user connects, Cloudflare auto-provisions accounts based on the authenticated email from Stripe’s orchestrator platform. For existing users, a standard OAuth flow grants access to the Stripe Projects CLI. Credentials are stored securely and made available to agents for authenticated API requests. Third, payment via tokenization: Stripe includes payment tokens in requests to Cloudflare, but raw credit card details never reach the agent. The default spending limit is $100 USD per month, per provider.
The workflow looks like this:
stripe projects init
stripe projects add cloudflare/registrar:domain
# Agent now has account, domain, API token—ready to deployThat’s “one-shot” provisioning. After you accept the Terms of Service once, the agent handles everything: account creation, domain purchase, API token generation, deployment. Consequently, no copy-pasting credentials and no human in the loop.
The Agentic Economy: Stripe’s 288-Product Bet
However, Cloudflare isn’t the only player here. At Stripe Sessions 2026 on April 30, Stripe announced 288 product launches building what they call “economic infrastructure for AI.” The Agentic Commerce Suite includes the Machine Payments Protocol (MPP) for programmatic transactions, Shared Payment Tokens (SPTs) that let agents initiate payments without exposing credentials, and Link Digital Wallet integration where agents make purchases on behalf of users using one-time-use cards per task. Additionally, Stripe introduced streaming payments—an AI-native business model combining precise usage tracking with stablecoin micropayments on the Tempo blockchain.
This is a platform play. Stripe isn’t just enabling agents to buy Cloudflare services. Instead, they’re positioning as the payment layer for agents to be economic actors across the entire internet. Furthermore, Google announced a partnership on agentic commerce the same day. Payment authorization unlocks true agent autonomy, and Stripe is racing to own that infrastructure layer.
If agents can be paying customers today, what comes next? Contract signing? Legal standing? The “agentic economy” where software entities have economic agency is no longer speculative. It’s shipping in production.
Are We Ready? Security Experts Say No
Security experts aren’t celebrating. David Shipley of Beauceron Security warned that this capability is “a huge win for cyber criminals” because it accelerates malicious infrastructure deployment. The technology is innovative for legitimate developers, but threat actors gain the same speed advantages. Meanwhile, Shashi Bellamkonda of Info-Tech Research Group highlighted operational complexity: “When provisioning or billing issues arise, businesses must have clearly defined process for resolving them with all parties.” His assessment? This emerging model “requires considerable upfront thought” before implementation—and enterprises aren’t there yet.
The legal reality compounds the risk. California’s AB 316, which took effect January 1, 2026, prevents defendants from using an AI system’s autonomous operation as a defense to liability claims. If your agent deploys malicious code or racks up unexpected bills, you can’t argue you lacked control. You’re liable, period. Furthermore, Palo Alto Networks predicted that by 2026, the gap between AI adoption speed and security preparedness would trigger the first major lawsuits, with executives held personally responsible for rogue AI actions.
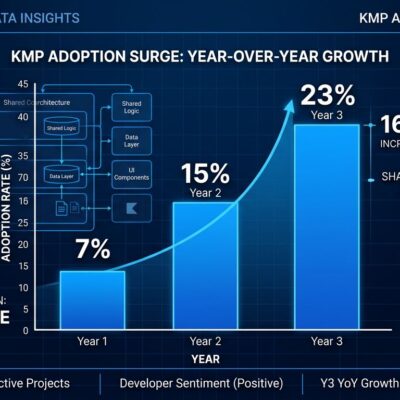
The statistics back up the concern. A C1 survey found 95% of enterprises now run AI agents autonomously, and non-human identities are expected to exceed 45 billion by the end of 2026—twelve times the human workforce. Yet only 10% of organizations report having a strategy for managing these autonomous systems. The governance gap isn’t just large. It’s massive.
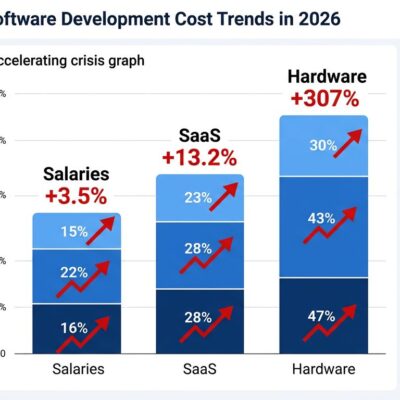
The $400M FinOps Gap: Visibility Isn’t Control
The $100 per month spending limit sounds reasonable until you consider how agents actually spend. They burn through budgets via model calls, retry loops, tool invocations, delegation, and replanning. A single debugging session with cascading retries can exhaust the monthly cap in hours. Traditional monitoring shows what agents spent—retrospective dashboards, cost attribution reports. However, runtime governance controls what agents CAN spend through preventive circuit breakers.
The industry is scrambling to build “runtime spend rails.” Before any consequential action—model call, tool invocation, infrastructure deployment—the agent requests authorization. The system atomically checks max_steps, max_seconds, max_tool_calls, and max_usd, then returns ALLOW, ALLOW_WITH_CAPS, or DENY. Waxell reports a “$400M AI FinOps gap” because cost visibility and cost control are fundamentally different capabilities. Moreover, Oracle, Agent Patterns, and Runcycles are all shipping runtime governance frameworks, but adoption lags deployment.
The Hacker News discussion (356 points, 199 comments) revealed the split. The pro-autonomy camp argues agents need payment authorization to be truly useful, and friction kills workflows. In contrast, the pro-control camp warns we’re enabling autonomy before building safeguards. The pragmatists note that enterprises won’t adopt this until there’s a compliance framework, audit trail, and clear liability model. All three camps are right.
Key Takeaways
- AI agents can now autonomously create Cloudflare accounts, buy domains, and deploy apps through a new protocol announced April 30, 2026
- Payment authorization via Stripe tokenization unlocks true agent autonomy—agents are customers, not just tools using your credentials
- Stripe launched 288 products at Sessions 2026, positioning as the payment layer for the emerging “agentic economy”
- Security experts warn this accelerates malicious infrastructure deployment, and California AB 316 makes you liable for agent actions regardless of autonomous operation
- The governance gap is massive: 95% of enterprises run agents autonomously, 45 billion non-human identities expected by year-end, but only 10% have management strategies
- Runtime spend control (preventive circuit breakers) is critical, but industry adoption lags—cost visibility from dashboards doesn’t prevent runaway spending