Google Project Zero published a complete zero-click root exploit chain for the Pixel 10 this week, and the story isn’t just about a single bug — it’s about a pattern that keeps repeating. Researchers Seth Jenkins and Jann Horn chained CVE-2025-54957 (a Dolby audio decoder vulnerability) with a newly discovered VPU kernel driver flaw to achieve full device root access with no user interaction required. Both bugs are now patched. The deeper question is why the same class of vulnerability keeps appearing in successive Pixel generations.
How the Attack Works: Audio File to Root in Two Steps
The attack requires zero user interaction — no tapping, no opening an attachment, nothing. When a malicious audio file arrives via Google Messages, Android’s transcription service processes it automatically in the background. That background processing is the entry point. CVE-2025-54957 exploits the Dolby Unified Decoder (UDC) during this silent transcription, achieving remote code execution in the Dolby process before the user sees the notification.
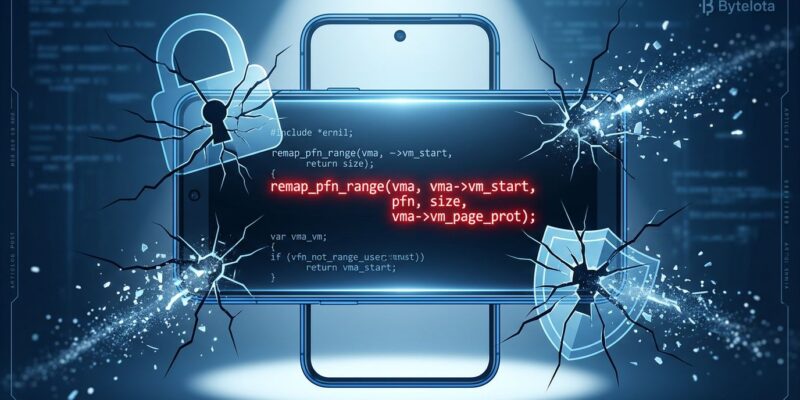
Stage 2 escalates to the kernel. The Pixel 10’s Tensor G5 chip includes a new video processing unit driver at /dev/vpu (Chips&Media Wave677DV). The driver’s mmap handler contains a straightforward bounds-checking failure:
return remap_pfn_range(vm, vm->vm_start, pfn,
vm->vm_end-vm->vm_start, vm->vm_page_prot);
// Mapping size is user-controlled VMA with no bounds checkAn attacker can request a mapping larger than the hardware register region, which maps kernel memory directly into userspace. On Pixel devices, the kernel sits at a predictable physical address — KASLR randomizes virtual addresses but not physical ones — so arbitrary kernel read-write requires just five lines of code once this mapping is achieved. Full root access follows.
The Pattern That Won’t Die
The Pixel 9 had a similar privilege escalation vector through the BigWave driver. When Project Zero reported those issues, the reasonable expectation was that the same development team would audit their other drivers before shipping new hardware. Instead, the same team wrote the VPU driver for the Pixel 10’s Tensor G5 — and five months after the BigWave disclosure, Jenkins described finding the VPU flaw as “immediately apparent” during a cursory review. The escalation stage took under two hours to discover and develop.
This isn’t a one-off mistake. It’s a process gap. Hardware driver code that exposes kernel memory through unconstrained remap_pfn_range calls has appeared in BigWave, the VPU driver, and similar issues have surfaced in Mali GPU and NPU drivers. Patching the Pixel 9 exploit didn’t close the zero-click attack surface — it just forced researchers to find the next privilege escalation primitive in the new hardware stack.
Related: Fragnesia CVE-2026-46300: The Dirty Frag Patch Backfired — another example of a patch that introduced a new exploitation path.
AI Features Are Expanding the Zero-Click Attack Surface
The Dolby decoder is exploitable at zero-click precisely because Android processes audio for AI transcription before users open their messages. That’s a deliberate product decision. As discussion of this research noted: “Over the past few years, several AI-powered features have been added to mobile phones… One effect of this change is increased 0-click attack surface.” Every silent media parsing operation — audio transcription, message previews, image recognition in notifications — is a potential entry point for this class of attack.
Apple’s response with Lockdown Mode takes the opposite approach: disable all media previews entirely. It’s an acknowledgment that rich AI features and zero-click safety are fundamentally in tension. Android hasn’t made that trade-off explicit. As long as audio transcription and media enrichment run before user interaction, the Dolby-style entry point (or its successor) remains part of the attack surface.
Pixel 10 Patch Status: What Developers Need to Know
Both vulnerabilities are patched. CVE-2025-54957 was addressed across all Android in the January 2026 Android Security Bulletin. The VPU kernel driver bug was fixed in the February 2026 Pixel update — 71 days after Project Zero’s November disclosure, which Project Zero noted as remarkably fast for a driver vulnerability. The May 2026 Pixel Update Bulletin provides full protection and includes a bootloader increment that prevents rollback to vulnerable builds.
The caveat: 42% of Android devices never receive security updates. Pixel users have access to the patch — the question is whether they’ve applied it. Fleet managers and enterprise Android developers should treat this as a priority deployment, not an optional update. The Hacker News discussion around this research surfaced that this 71-day turnaround may be the first Android driver vulnerability patched within 90 days — encouraging, but it doesn’t help the majority of Android devices that never receive updates at all.
Key Takeaways
- Update Pixel 10 devices to the May 2026 build immediately — both the Dolby (CVE-2025-54957) and VPU vulnerabilities are fully patched
- Zero-click attacks don’t require user error; they exploit background media processing that runs before any user interaction
- Android hardware driver security has a recurring gap: the same class of unbounded
remap_pfn_rangebug has appeared in multiple driver generations from the same development team - AI features that silently process incoming media are zero-click attack surface by design — expect this pattern to continue as Android adds more ambient intelligence