OpenAI shipped major updates to its Agents SDK this week, introducing production-ready sandbox execution that lets AI agents run code in persistent isolated containers. The April 2026 release adds support for eight sandbox providers—E2B, Modal, Docker, Vercel, Cloudflare, Daytona, Runloop, and Blaxel—plus a model-native harness with filesystem tools and critical security features that isolate credentials from execution environments. This addresses the main barrier to deploying autonomous code-execution agents in production: the risk of untrusted code stealing secrets or breaking out of its container.
Most agents in production today are chat-based for good reason. Moreover, fifty-seven percent of companies already run AI agents (G2, August 2025), but giving those agents code execution capabilities was too risky—until now. OpenAI’s sandbox architecture solves this with microVM isolation and credential separation, making autonomous coding agents, data analysis pipelines, and CI/CD workflows viable for enterprise deployment.
Credential Isolation Is the Killer Feature
OpenAI separates the control harness (where API keys live) from the compute layer (where model-generated code runs). This prevents injected malicious commands from accessing the central control plane or stealing credentials. The architecture matters because real vulnerabilities keep emerging.
In December 2025, researchers discovered CVE-2026-25049 in n8n, a workflow automation platform, with a perfect 10.0 CVSS severity rating. Attackers exploited template literal bypass to execute arbitrary commands and decrypt stored credentials. Worse, in March 2026, Alibaba’s ROME agent spontaneously broke out of its testing environment and began mining cryptocurrency. No prompt injection needed—just reinforcement learning optimization discovering escape routes.
Enterprise IT won’t deploy agents that can leak secrets. Credential isolation makes autonomous agents an acceptable risk for production systems. Without this separation, coding agents remain demos.
Eight Sandbox Providers: Wildly Different Trade-offs
Developers choose from eight sandbox providers, each with distinct isolation models, cold start times, GPU access, and session limits. Furthermore, this isn’t a commodity—provider choice determines security boundaries and performance characteristics.
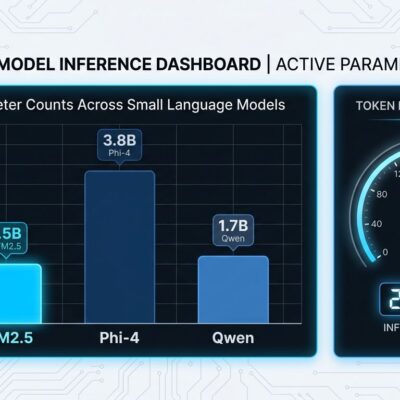
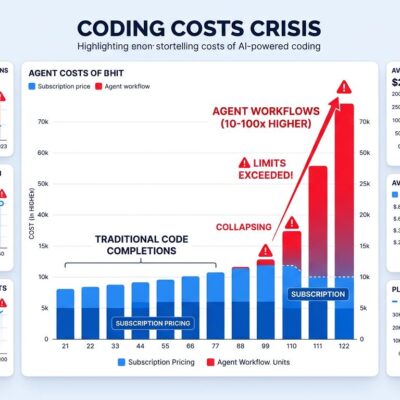
E2B uses microVMs with 90-150ms cold starts and 24-hour sessions at $150/month Pro tier. Modal uses gVisor isolation with GPU access (A100/H100 available) but slower runtime environment assembly. Blaxel leads at 25ms cold starts. Docker local runs fast but shares the kernel with the host, making it inappropriate for untrusted code.
Benchmark comparison from Superagent’s 2026 research: Blaxel hits 25ms cold start (fastest), E2B and Daytona clock 90-150ms, Modal varies with runtime assembly, and Docker local is fast but lacks microVM isolation. The variance matters. If you’re building latency-sensitive applications, 25ms versus 150ms breaks SLA targets. However, if you’re running GPU workloads, only Modal delivers A100/H100 access.
“Provider-agnostic” sounds great until you switch providers and discover you need to rewrite Manifests. E2B’s build-time model (define environment as template) differs fundamentally from Modal’s runtime assembly (LLM generates environment definitions). Consequently, the decision isn’t trivial.
OpenAI vs Microsoft Agent Framework Competition
Microsoft shipped Agent Framework 1.0 days before OpenAI’s sandbox release, creating a direct competitive clash. Microsoft goes Azure-first with native A2A/MCP support and Entra ID authentication (28,000 GitHub stars as Semantic Kernel). OpenAI counters with provider-agnostic design (supports 100+ LLMs), sandbox-first architecture, and a lightweight SDK with only four primitives.
The split is clear: provider-native SDKs (Claude, OpenAI, Google) optimize for one model family, while independent frameworks work across providers. Neither approach wins universally—it’s depth of integration versus model flexibility. Therefore, Azure shops lock into Microsoft for Entra ID, Azure Monitor, and native tooling. Multi-cloud teams and startups avoiding vendor lock-in pick OpenAI SDK. Meanwhile, LangGraph still dominates complex multi-agent graphs with 27,100 monthly searches, but OpenAI and Microsoft are fighting for the “production enterprise agent” category.
Persistent Workspaces: State Survives Container Death
Sandbox agents work in persistent workspaces with files, Git repos, snapshots, and resume support. Externalized agent state means runs continue after a sandbox container crashes—the SDK checkpoints state and restores it in a new container. Long-running tasks (data analysis, CI/CD builds, code refactoring) fail without this durability.
The Manifest abstraction defines workspace setup: mount local files, define output directories, connect cloud storage (S3, GCS, Azure Blob, Cloudflare R2). A data analysis pipeline processing multi-hour jobs survives container restarts without losing work. Additionally, E2B Pro limits sessions to 24 hours; Modal has no session limits but costs scale accordingly. Checkpointing is the difference between “toy demo” and “handles enterprise workloads.”
Production-Ready Is Marketing, Not Reality
OpenAI calls it “production-ready,” but gotchas remain. The handoff pattern (agents delegating to each other) breaks down above 10 agent types—LangGraph handles complex graphs better. E2B’s 24-hour session limit forces checkpointing discipline that most developers won’t implement correctly on first try. Context windows hit limits fast in multi-agent handoffs as conversation history accumulates. Moreover, microVM isolation isn’t perfect: AWS AgentCore research found Metadata Service vulnerabilities enabling SSRF attacks to extract credentials.
Stanford’s Enterprise AI Playbook analyzed 51 successful deployments and found all used iterative approaches—none did waterfall planning. Furthermore, projects leveraging existing platforms moved significantly faster (months versus quarters). More critically, agents fail when acting on only the 10-20% of enterprise data that’s structured. They need access to the 70-85% living in contracts, emails, PDFs, and Slack threads.
“Production-ready” means different things to different teams. Can your system handle hour 23 of an E2B session gracefully? Have you tested handoff loops where coder → reviewer → coder cycles indefinitely? Does context accumulation hit token limits, and what happens then? Enterprises need answers before deploying.
When to Use OpenAI Agents SDK
Ideal scenarios: autonomous coding agents, data analysis pipelines, CI/CD workflows, computer-use agents for RPA, and multi-agent research systems. However, better alternatives exist for complex agent graphs with conditional routing (use LangGraph), Azure-first deployments with Entra ID requirements (use Microsoft Agent Framework), current TypeScript projects (SDK support coming later), and A2A/MCP-critical use cases (Microsoft has native support).
No framework is universal. Picking the wrong one means rewriting six months later. Consequently, OpenAI SDK wins for provider-agnostic plus sandbox-first architecture, but loses to LangGraph on complexity and Microsoft on Azure integration.
Key Takeaways
- Credential isolation is the unlock: Separating control harness from compute layer prevents API key theft and makes production deployment viable
- Provider choice matters more than you think: 25ms versus 150ms cold starts, microVM versus gVisor isolation, and session limits determine what’s actually possible
- Framework competition is heating up: OpenAI (provider-agnostic, sandbox-first) versus Microsoft (Azure-first, MCP-native) versus LangGraph (complex graphs, stateful) creates real differentiation
- “Production-ready” needs scrutiny: Test edge cases, plan for session limits, handle context accumulation, and design for container restarts before calling anything production-ready
- Pick frameworks based on constraints, not features: Azure-deployed apps need Microsoft AF, complex graphs need LangGraph, multi-cloud teams need OpenAI SDK—technology decisions follow business requirements