Vercel disclosed a security incident on April 19, 2026, involving unauthorized access to internal systems that potentially exposed customer environment variables. A limited subset of customers were impacted, though exact numbers remain undisclosed. According to industry sources, Vercel’s internal tools including Linear and GitHub were compromised, but environment variables marked as “sensitive” using Vercel’s encryption feature appear to have been protected. Services remain operational, and Vercel engaged incident response experts and law enforcement.
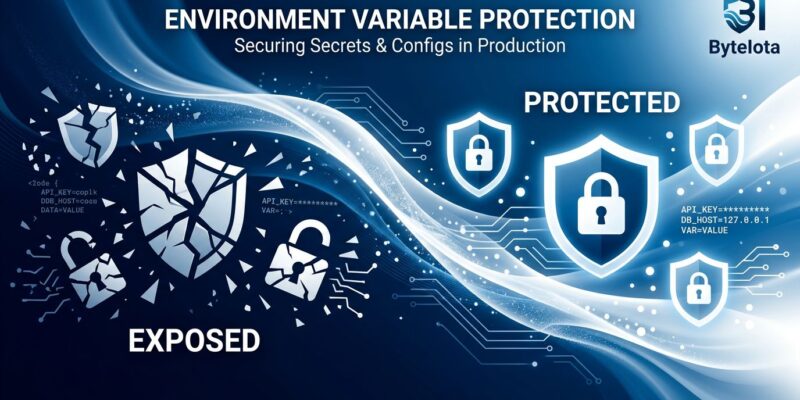
Sensitive Environment Variables: The Critical Distinction
Vercel offers a “sensitive environment variable” feature that encrypts specific secrets and stores them separately from standard environment variables. According to Theo of t3.gg, environment variables marked as “sensitive” were NOT compromised in this breach, while non-sensitive variables may have been exposed. This distinction likely prevented a far worse outcome.
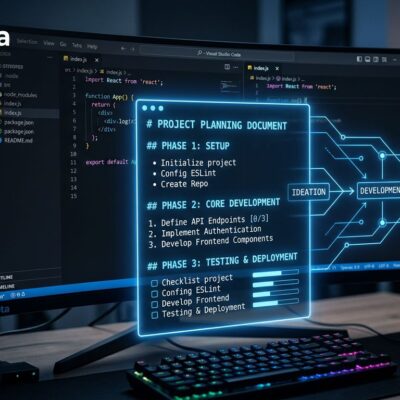
The feature exists but many developers don’t use it by default. To enable it via CLI:
# Mark critical secrets as sensitive (encrypted, non-readable)
vercel env add DATABASE_URL production --sensitive
vercel env add STRIPE_SECRET_KEY production --sensitive
vercel env add AWS_SECRET_ACCESS_KEY production --sensitiveOnce marked sensitive, values become non-readable even to project owners and can only be used in Production and Preview environments. You cannot edit sensitive variables after creation—you must delete and recreate them to change values.
API keys for Stripe, database credentials, and OAuth secrets marked “sensitive” appear safe. However, any secrets stored as regular environment variables may be at risk. If you didn’t know about or use this feature, you face potential exposure.
Immediate Actions: Rotate Non-Sensitive Secrets Now
Vercel recommends all customers—not just those directly notified—review environment variables and rotate non-sensitive secrets immediately. The vague “limited subset of customers” language means you cannot assume safety just because you haven’t been notified.
Take these actions now:
- Rotate ALL non-sensitive environment variables (API keys, database URLs, auth tokens)
- Enable sensitive environment variable feature for critical production secrets
- Audit deployment logs for unauthorized access
- Review access controls (who can view/modify environment variables)
- Check downstream services (Stripe, AWS, databases) for suspicious activity
Security experts at GitGuardian warn that “rotating secrets stored in your CI/CD platform is not enough—you must hunt for malicious actions on all your integrated SaaS and cloud platforms.” Exposed environment variables don’t announce themselves. Attackers could be using stolen credentials RIGHT NOW to access databases, make API calls, or exfiltrate data. Consequently, waiting for confirmation wastes critical response time.
Supply Chain Attack Pattern: Platforms as Vectors
This breach follows a surge of supply chain attacks in March 2026, with five major incidents in just 12 days. The Axios NPM package compromise, attributed to North Korean threat actors, deployed cross-platform malware. Moreover, TeamPCP hacking group compromised Trivy, KICS, LiteLLM, and Telnyx—all security and development tools developers trust.
When platforms like Vercel are compromised, thousands of downstream customers inherit the risk. Cybercrime has shifted from isolated intrusions to ecosystem-wide compromises. Attackers target trusted vendors to gain “inherited access” to hundreds of organizations at once.
Other 2026 platform incidents include n8n CVE-2026-25049 (template bypass with 10.0 CVSS severity) and Docker CVE-2026-34040 (critical auth bypass). Platform breaches are uniquely dangerous because they multiply—one Vercel compromise affects thousands of customer applications.
Limited Disclosure Raises Questions
Vercel’s security bulletin provides minimal technical details. No disclosure of the attack vector. No specific timeline of when the breach occurred (only when disclosed). No definition of “limited subset of customers.” Furthermore, no specifics on what “internal systems” were compromised.
What we don’t know matters:
- How many customers affected (“limited subset” tells us nothing)
- Attack method (credential stuffing? supply chain? insider threat?)
- Timeline (when did breach occur vs when discovered?)
- Scope (what does “internal Vercel systems” mean?)
- Whether source code or customer deployment data was accessed
Lack of detail makes it impossible to assess true risk. Developers cannot make informed decisions about whether to migrate, what secrets to rotate, or how urgently to respond. Transparency builds trust; vague statements raise more questions than answers. Additionally, CircleCI provided detailed technical post-mortems after their breach, including attack vectors and forensic timelines. Vercel’s minimal disclosure falls short of that standard.
Key Takeaways
- Sensitive environment variables feature worked as intended: Vercel’s encryption separated sensitive secrets from standard env vars, likely preventing worse damage
- Rotate non-sensitive environment variables immediately: Don’t wait for notification—proactive rotation limits exposure window
- Supply chain attacks are escalating in 2026: Five major incidents in March alone, platforms are prime targets, downstream customers inherit risk
- Transparency gap is concerning: Vague “limited subset” language and lack of technical details prevent informed risk assessment
- Defense-in-depth is mandatory: Platform breaches prove you cannot rely solely on vendor security—use secrets managers, automate rotation, implement zero-trust architecture