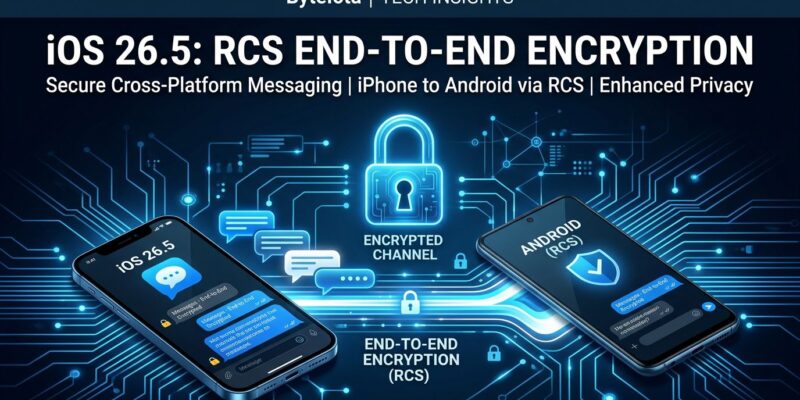
For years, texting between an iPhone and an Android was a quiet privacy failure. iMessage? Encrypted. Signal? Encrypted. Your cross-platform RCS threads — the ones that replaced SMS but never inherited its successor’s security — readable by carriers, platforms, and anyone with network access. iOS 26.5, released May 11, closes that gap. Apple and Google jointly shipped end-to-end encrypted RCS messaging, on by default, built on a real IETF standard. The long embarrassment is over.
What Shipped in iOS 26.5
The feature is part of a broader iOS 26.5 release, but the E2EE RCS update is the one that matters. Encryption rolls out in beta for iPhone users on iOS 26.5 and Android users on the latest Google Messages — automatically enabled for new and existing RCS conversations once both parties are on supported carriers. Users see a lock icon when a thread is encrypted. No lock means fallback to unencrypted RCS.
The joint rollout is notable. Apple and Google — two companies that compete aggressively on almost everything — co-authored the encryption specification and shipped simultaneously. Credit where due: that coordination is hard and it worked.
The Protocol Under the Hood: MLS
The encryption uses Messaging Layer Security (MLS), standardized as IETF RFC 9420. If you’ve built anything with encrypted group messaging, MLS is worth understanding — it’s the protocol Meta already adopted for WhatsApp and Messenger, and it’s now the backbone of RCS E2EE.
The core mechanism is a ratchet tree: a binary tree of public keys maintained per group per client. Each message epoch derives a new Group Secret, which produces per-sender Ratchet Secrets, which produce per-message AEAD encryption keys. Each message advances the ratchet forward — you can’t compute an old key from a new one. This gives you:
- Forward secrecy: a compromised key today doesn’t decrypt past messages
- Post-compromise security: fresh key updates heal the group after a breach
- Efficient scaling: adding or removing a group member requires log(N) operations, not N
The GSMA’s RCS E2EE spec also notes post-quantum cryptography algorithm support, making MLS more future-resistant than older approaches. For developers building encrypted group communications, MLS is the IETF-blessed reference implementation to evaluate right now.
RCS Universal Profile 3.0: The Standard Behind the Standard
The interoperability piece — how an Apple server and a Google server exchange MLS key material without either platform reading your messages — is defined in GSMA’s RCS Universal Profile 3.0, published March 2025 with Apple as a co-author. UP 3.0 specifies client-side encryption and decryption, MLS group synchronization with RCS chats, key delivery between providers, and error handling for failed key exchange.
Beyond encryption, UP 3.0 also standardizes cross-platform message editing, message deletion, Tapback reactions, and inline replies — things that previously only worked within the same platform. RCS is finally approaching feature parity with dedicated messaging apps.
The Catch: Carrier Support
Here’s what the press releases understate: E2EE only activates when both parties use carriers that support UP 3.0. If your carrier or your recipient’s carrier hasn’t updated, you get unencrypted RCS or SMS — no error, no warning beyond the missing lock icon. 9to5Mac has the current carrier list, which is incomplete at launch.
At launch, the rollout is beta and geographically uneven. UK carrier support is unclear. Even on supported carriers, not every user gets the feature immediately. Fragmentation is the RCS ecosystem’s chronic condition, and E2EE doesn’t fix that underlying problem.
What This Actually Changes for Developers
A few things worth knowing:
- No new iOS APIs for RCS E2EE. It lives entirely inside Messages.app at the system level. Third-party apps don’t get access.
- A2P messaging is unaffected. Business-to-user RCS (OTPs, notifications, marketing campaigns) runs on different infrastructure. UP 3.0’s E2EE covers P2P only.
- Third-party messaging apps won’t lose users overnight, but the encryption argument weakens as a differentiator. Compete on features: disappearing messages, cross-device sync, communities.
- MLS is worth studying. If you’re building encrypted communications for any platform, RFC 9420 is the current standard. Signal’s Double Ratchet scales differently; MLS wins on group operations.
One caveat from security researchers: Privacy Guides notes that RCS E2EE uses shorter-lived session keys rather than long-term identity verification — the approach Signal uses with safety numbers and QR code verification. For most users, this is fine. For high-risk scenarios — journalists, activists, anyone who needs to verify they’re talking to the right person — Signal or iMessage remain stronger choices.
The Bottom Line
iOS 26.5’s encrypted RCS is a meaningful infrastructure upgrade that most users will never think about — and that’s exactly how it should work. The technical foundation (MLS, UP 3.0) is solid. The cooperative execution (Apple + Google shipping together) is genuinely impressive. The carrier fragmentation is real and will take time to resolve.
SMS took decades to die. Its replacement finally has the security story it needed. That’s progress worth acknowledging, even if Signal isn’t worried about its users leaving.