In March 2026, engineer Alisher Khojayev published complete blueprints for a shoulder-fired guided missile on GitHub—built for $96 using a 3D printer and an ESP32 chip you’d find in a smart doorbell. The MANPADS (Man-Portable Air-Defense System) prototype includes GPS guidance, ballistics calculations, and a flight computer, all detailed in a repository treating weapons design like it’s a JavaScript framework. Traditional MANPADS cost $20,000-$100,000 and require military manufacturing. This costs less than a video game and can be printed at home. This isn’t another “3D-printed gun” story. It’s the moment open-source culture’s libertarian ethos collides head-on with weapons proliferation—and none of the existing frameworks are remotely equipped to handle it.
Arms Control Built for 1990s Can’t Stop GitHub Repos
The Missile Technology Control Regime (MTCR) and Nuclear Suppliers Group (NSG) were designed in the 1990s to control physical manufacturing and exports. In 2016, the MTCR acknowledged “3D printing technology poses a major challenge to international export control efforts”—and then did nothing. Eight years later, you can download MANPADS designs as easily as a React template.
The policy gaps are comprehensive. The MTCR controls maraging steels but not in powder form, which is exactly what 3D printing uses. Only the Wassenaar Arrangement added “additive manufacturing equipment” controls in 2016, but the scope was narrow—turbine blades only, nothing about guidance systems. Export controls can’t detect digital file transfers. There are no borders to monitor, no ports to inspect, no physical smuggling to interdict. Sanctioned countries like North Korea can bypass physical goods restrictions entirely by downloading a GitHub repository.
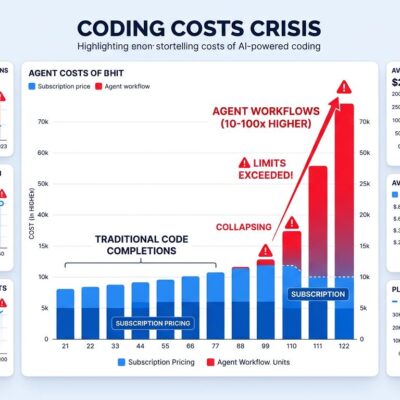
Cost barriers and manufacturing restrictions were the entire basis of arms control. When a $96 missile performs comparably to a $20,000 one, and the blueprint is a GitHub link, every assumption underlying global security frameworks breaks down. Intelligence agencies can’t track what they can’t see.
GitHub’s Dual-Use Policy Was Written for Bugs, Not Bombs
GitHub’s Acceptable Use Policy prohibits “unlawful attacks” but explicitly allows “publication of dual-use content for security research.” The entire framework assumes software vulnerabilities—a researcher finds a bug, notifies the vendor, waits 90 days, then publishes. You can’t “patch” a weapons design. There’s no vendor to notify. The “abuse” IS the intended use.
The responsible disclosure model that works for software completely breaks down here. USENIX Security 2026 standards require researchers to “disclose vulnerabilities to benefit users.” Publishing cryptography code helps people protect their privacy. Publishing MANPADS blueprints helps… whom, exactly? GitHub’s core principle is that “code remains available unless there’s a clear basis for removal”—a policy written for JavaScript libraries, not guided missiles.
The responsibility vacuum is total. The creator frames it as “educational.” The platform says it’s “just hosting code.” The community invokes “information wants to be free.” Nobody is accountable when that GitHub repo gets used to shoot down a civilian aircraft. Platforms designed for collaboration and openness have no coherent framework for weaponry, and their default position—leave content up unless forced to remove it—is absurd when applied to weapons systems.
When “Information Wants to Be Free” Becomes “Weapons Want to Proliferate”
The maker community’s libertarian ethos comes from Stewart Brand’s 1984 quote: “Information wants to be free.” Everyone forgets the full quote: “On the one hand information wants to be expensive, because it’s so valuable. On the other hand, information wants to be free, because the cost of getting it out is getting lower.” It’s a nuanced economic observation, not an absolutist mandate. More importantly, the cypherpunks applied it to cryptography—defensive technology enabling privacy and resisting censorship—during the 1990s Crypto Wars when the US government tried to classify encryption as munitions.
Publishing PGP source code helped people resist surveillance. Publishing MANPADS blueprints helps… what, exactly? The ethical framework that worked for cryptography doesn’t transfer to weaponry. Cryptography enables defense—privacy, security, resistance to authoritarian surveillance. Guided missiles enable offense—violence, destruction, targeting of people and assets. The distinction matters.
The maker community is applying a principle designed for privacy tools to weapons guidance systems, without recognizing the fundamental difference. Research papers on explosives chemistry require expertise to implement and reach limited academic audiences. GitHub blueprints are step-by-step enablement for anyone with a 3D printer. Context matters, but the “information freedom” camp treats all bits as equivalent, as if publishing encryption algorithms and publishing missile guidance code are the same category of speech. They’re not.
Ukraine’s FPV Drones Show What’s Possible—And What’s Responsible
Ukraine produces 5 million FPV (First-Person View) drones annually at ~$400 each, using them to destroy multimillion-dollar Russian assets. Over half of frontline destruction comes from these DIY weapons, built by volunteers and soldiers—many were hobbyists pre-war—using commercially available racing drone frames with anti-tank grenades strapped on. The production scale is staggering: 150+ manufacturers ranging from mom-and-pop shops to industrial operations, 90% of units supplied by volunteers or military units rather than traditional defense contractors.
The innovation is real. Fiber optic tethers defeat Russian jamming. Open-source ArduPilot software enables sophisticated guidance. The Pentagon is now buying Ukrainian interceptor drones, and Ukraine is exporting its technology internationally. This is the largest-scale demonstration of democratized weaponry in modern warfare, and it proves the DIY missile concept isn’t theoretical—it works.
But there’s a critical difference. Ukraine demonstrated practical feasibility in a defensive wartime context. They did NOT publish step-by-step blueprints on GitHub for global download. Capability demonstration is not the same as proliferation platforming. You can acknowledge that democratized weapons technology is inevitable—the genie IS out of the bottle—while still choosing not to amplify it. Ukrainian volunteers building drones to defend their country is fundamentally different from publishing MANPADS designs on a platform accessible to any bad actor with an internet connection.
It’s Not About Banning Information—It’s About Choosing What to Amplify
The Hacker News discussion shows the community divided between free speech absolutists (“information can’t be controlled”) and security hawks (“this enables terrorism”). Both miss the point. The real question isn’t whether we can stop this information from existing—we can’t—or whether all weapon information should be banned—that’s impractical. The question is about platforming and amplification.
Should GitHub host MANPADS designs the same way it hosts React components? Should we treat weapons blueprints like JavaScript frameworks? The Hacker News debate includes supporters arguing “technology democratization enables resistance against authoritarian states,” citing Afghan Mujahideen and Vietnamese civilians—controversially, also David Koresh. Critics warn about ITAR implications and enabling dangerous actors. Technical skeptics argue cheap sensors lack reliability, while asymmetric warfare realists counter that volume compensates for individual unit unreliability. The most upvoted comment (441 points) shared a historical anecdote about Soviet missiles using simple light-dependent resistors, suggesting sophisticated components aren’t necessary.
The distinction between “this information exists somewhere” and “GitHub actively hosts and distributes it” matters. Academic papers on explosives chemistry exist behind university access. Cryptography research gets published after responsible disclosure windows. We already make these distinctions all the time, but the maker community’s libertarian roots resist any line-drawing because “slippery slope.” The slippery slope is real. So is the harm from doing nothing. Choosing not to platform weaponry on code hosting sites doesn’t mean banning security research or suppressing academic freedom—it means recognizing that guidance systems for missiles aren’t the same category as encryption libraries.
Key Takeaways
- Arms control frameworks (MTCR, NSG) are obsolete for the digital-file era—you can’t control what you can’t see, and GitHub repos don’t go through customs
- Platform policies designed for software vulnerabilities completely break down when applied to physical weapons—responsible disclosure assumes a vendor to notify and a patch to deploy, neither of which exist for MANPADS
- “Information wants to be free” was about cryptography (defense: privacy, security) during the Crypto Wars, not guided missiles (offense: violence, destruction)—the ethical framework doesn’t transfer
- Ukraine’s 5 million FPV drones annually prove DIY weapons work at scale, but they demonstrated capability without publishing global blueprints—the distinction between feasibility and platforming matters
- The choice isn’t “ban all weapon information” versus “publish everything freely”—it’s about responsible platforming decisions that distinguish between security research and proliferation enablement
Open-source culture’s libertarian ethos worked brilliantly for privacy tools and encryption. It fails catastrophically when applied to weapons guidance systems. Platforms, communities, and creators need to recognize that not all bits are equal, and choosing what to amplify—versus merely acknowledging it exists—is an ethical decision with real consequences. The MANPADS repository might be educational for one person and operational for another, but GitHub isn’t equipped to make that distinction, and pretending the problem doesn’t exist won’t make it go away.