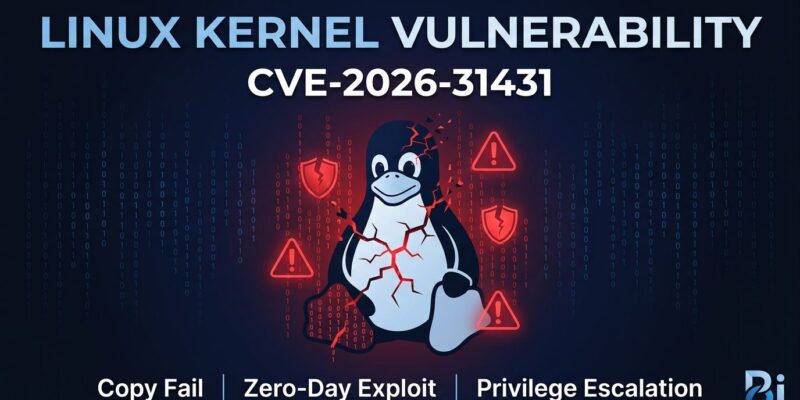
Security researchers at Theori publicly disclosed CVE-2026-31431 on April 29, revealing a 9-year-old Linux kernel zero-day that lets any authenticated user gain root access on virtually every distribution shipped since 2017. The exploit? A 732-byte Python script. Unlike Dirty Cow or Dirty Pipe, which required winning race conditions, Copy Fail is a straight-line logic flaw—deterministic and reliable. Three days later, no major distribution has shipped kernel patches, and cloud providers remain silent.
Why Copy Fail Is Terrifyingly Simple
Most privilege escalation vulnerabilities depend on race conditions—narrow timing windows where attackers must outpace the kernel. Dirty Cow and Dirty Pipe required retries and often failed unpredictably. Copy Fail works every time. The technical analysis from Xint shows the same 732-byte Python script roots Ubuntu, RHEL, Amazon Linux, and SUSE without per-distro offsets. Solar Designer from Openwall verified it on Rocky Linux 9.7. No retries, no timing tricks—just a logic flaw in the algif_aead kernel module that writes 4 bytes into the page cache of any readable file.
Theori’s summary: “Chain it with anything that gives you local code execution and you’re root.” Any container RCE becomes instant host compromise. Any malicious GitHub Actions workflow roots the runner. Any web app vulnerability with local execution escalates to full system control. For cloud environments, CI/CD pipelines, and shared hosting, the barrier to exploitation is whether you can run code as a standard user.
How Crypto Code Hid a Logic Bug for 9 Years
The vulnerability lives in cryptographic code—the authencesn AEAD wrapper for IPsec security. A 2017 kernel optimization introduced in-place decryption to the algif_aead module, shaving milliseconds off crypto operations. The trade-off? A logic error where the kernel writes at offset assoclen + cryptlen without validating boundaries. When user buffers and page cache pages coexist in the same scatterlist, that write corrupts files in memory without marking them dirty. The file on disk stays intact, checksums pass, and the exploit remains invisible.
This flaw has been exploitable since 2017—through Ubuntu Bionic (18.04), Amazon Linux 2023, RHEL 10.1, Debian, and Arch. How did kernel review miss this for nearly a decade? Cryptographic code is complex, optimizations are subtle, and logic flaws don’t crash systems. Copy Fail worked silently until Theori reverse-engineered the exploit path.
Multi-Tenant Cloud Environments at Highest Risk
Cloud security assumes container isolation prevents privilege escalation. Copy Fail shatters that. An attacker with RCE inside a container—through a vulnerable dependency, misconfigured API, or supply chain compromise—escapes to the host with a single script. From there, they control the entire instance, access neighboring containers, and pivot across infrastructure.
CI/CD systems face identical exposure. GitHub Actions, GitLab CI, and Jenkins execute untrusted code from pull requests. If a malicious package lands in the build, Copy Fail grants root access. Kubernetes amplifies the risk: container escape leads to node compromise, then cluster admin privileges.
AWS, Azure, and GCP haven’t published Copy Fail advisories or patch timelines as of May 2. Managed services are likely patched silently, but customer EC2, VMs, and GKE nodes remain vulnerable. The Ubuntu Security Team released a workaround, and CERT-EU issued a high-severity alert, but cloud providers owe customers transparency.
What Developers Should Do Now
Don’t wait for patches. Apply the mitigation immediately on all Linux systems—development machines, staging, production, and especially multi-tenant infrastructure. The workaround disables the algif_aead module, forcing apps to use userspace crypto instead of hardware acceleration. Performance impact is negligible.
# Immediate mitigation (all distributions)
echo "install algif_aead /bin/false" > /etc/modprobe.d/disable-algif.conf
rmmod algif_aead 2>/dev/null || true
# Verify module is disabled
lsmod | grep algif_aead
# (should return nothing)Prioritize multi-tenant systems first: cloud instances, container hosts, Kubernetes nodes, CI/CD runners, shared hosting. Then development environments with SSH access. Most apps won’t notice—dm-crypt, LUKS, SSH, TLS, and IPsec use different code paths. Only apps explicitly using AF_ALG for AEAD ciphers fall back to userspace crypto.
Three Days Without Patches Is Unacceptable
The mainline kernel fix was committed April 1, 2026—nearly a month before public disclosure. Ubuntu, Red Hat, Debian, and SUSE received advance notification. Yet three days after the exploit went public, no major distribution has shipped kernel packages. Ubuntu released a kmod update to disable the module, but that’s a workaround. Red Hat says “patches pending.” Amazon Linux and Debian show the same status. Cloud vendors haven’t acknowledged the vulnerability publicly.
Compare this to Windows or macOS, where critical patches ship within 24-48 hours. The Linux ecosystem’s distributed model creates dangerous delays when exploits are public. Attackers don’t wait three days. When a reliable root exploit hits GitHub, the clock starts immediately. Every hour without patches is another hour of exposure for billions of systems.
The disclosure was responsible—researchers gave advance notice, and the mainline fix existed before disclosure. The failure is the patch delivery pipeline. Cloud providers should have preloaded patches and announced timelines within hours. Distributions should have shipped emergency updates within 24 hours. The Linux community needs to solve this structural problem.