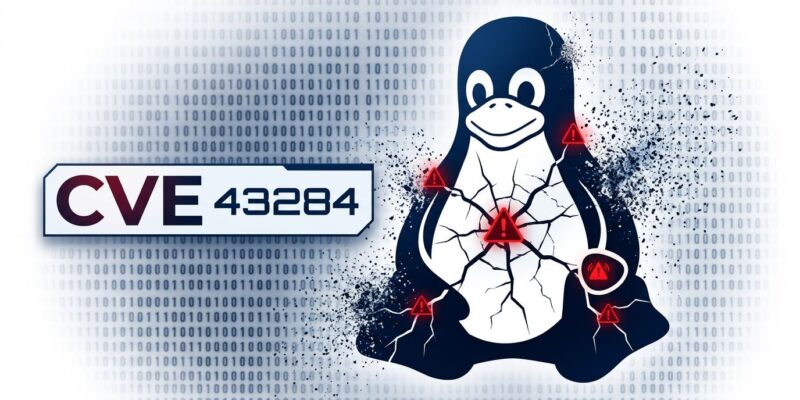
Linux systems face their second critical privilege escalation exploit in eight days. Dirty Frag (CVE-2026-43284, CVE-2026-43500), disclosed May 7, allows any unprivileged local user to gain root access on virtually all major distributions. A working public exploit is already available on GitHub, and Microsoft Security reports active but limited in-the-wild attacks. The disclosure came after a third party broke the responsible disclosure embargo, leaving thousands of production systems vulnerable before patches were ready.
This happened just one week after Copy Fail (CVE-2026-31431) was disclosed on April 29. Two major Linux root exploits in eight days raises uncomfortable questions about kernel security.
How Dirty Frag Works
Dirty Frag chains two page-cache write vulnerabilities in the Linux kernel—one in the IPsec ESP subsystem (code from 2017) and one in RxRPC (code from 2023). Unlike race-condition exploits that depend on timing windows, this is deterministic. It works consistently, with near-100% success rates.
The exploit manipulates the frag member of the kernel’s struct sk_buff to write to protected page-cache memory. This corrupts sensitive system files loaded in RAM. When a privileged process executes the modified file, the attacker gains root. Wiz Security calls it “deterministic and highly reliable, similar to previous vulnerabilities like Copy Fail and Dirty Pipe.”
The working proof-of-concept executes in one command: ./exp produces an instant root shell. Red Hat assigned both CVEs “Important” severity (CVSS 7.8). The modules affected—esp4, esp6, and rxrpc—are standard components in production Linux kernels.
The Embargo Controversy
Researcher Hyunwoo Kim reported Dirty Frag to kernel maintainers on April 30. The plan was coordinated disclosure after distributions prepared patches. However, an “unrelated third party” leaked exploit details publicly on May 7, collapsing the embargo.
Tom’s Hardware summarized the fallout: “No patches available, no warning given.” CVE-2026-43284 was patched in mainline kernel code, but CVE-2026-43500 (the RxRPC component) wasn’t even fixed upstream yet. Ubuntu stable releases remained vulnerable days later.
The broken embargo meant attackers got exploit code while defenders were still waiting for patches. That’s the worst-case scenario for responsible disclosure. Combined with Copy Fail eight days earlier, the pattern is troubling.
Active Exploitation Confirmed
Microsoft Security isn’t just warning about theoretical risk—they’re “actively monitoring limited in-the-wild activity.” Real attackers are using this right now. Moreover, the value proposition is clear: transform any local access into complete system control.
The attack path is straightforward. Attacker gains limited access (compromised SSH credentials, web shell on an application server, container escape). Run the Dirty Frag exploit. Get root. Deploy ransomware, exfiltrate data, establish persistence. Microsoft notes that “SSH access, web shells, containers, or low-privileged accounts” are all sufficient starting points.
This shifts the security model from “prevent initial access” to “assume breach.” Developers often think local access isn’t a concern. Web application vulnerabilities change that calculation immediately.
Related: cPanel CVE-2026-41940: 44K Servers Hit in Black Week
Patch Status and Immediate Actions
Distribution responses varied. AlmaLinux and Fedora shipped emergency patches within 24 hours. AlmaLinux 9 users need kernel-5.14.0-611.54.3.el9_7 or newer. Fedora 44 shipped kernel-7.0.4-200.fc44, which fixed both CVEs—including the RxRPC component before upstream mainline had a patch. That’s impressive response speed.
Ubuntu tells a different story. The sid (unstable) branch is patched (linux 7.0.4-1 or newer), but stable releases including 22.04 LTS and 24.04 LTS remained vulnerable as of May 9. Furthermore, administrators running Ubuntu LTS in production need temporary mitigations while waiting for official patches.
Red Hat provides two mitigation strategies. The first blocklists vulnerable modules:
printf 'install esp4 /bin/false\ninstall esp6 /bin/false\ninstall rxrpc /bin/false\n' \
> /etc/modprobe.d/dirty-frag-blocklist.confThis works but breaks IPsec VPNs and AFS file systems. The second option disables unprivileged user namespaces, which preserves IPsec but impacts Docker and Podman rootless containers. Choose based on your infrastructure dependencies.
First step: verify if vulnerable modules are loaded.
lsmod | grep -E 'esp4|esp6|rxrpc'If those modules aren’t loaded, your exposure is lower. If they are, patch immediately or apply mitigations. The 24-48 hour window for emergency kernel patches isn’t conservative—it’s necessary. Active exploitation is confirmed, and the public exploit is trivial to use.
The “Dirty” Exploit Pattern
Dirty Frag is the third major “Dirty” kernel exploit. Dirty COW (CVE-2016-5195) exploited copy-on-write race conditions in code that existed since kernel 2.6.22 from 2007. Dirty Pipe (CVE-2022-0847) corrupted pipe_buffer structures with high reliability. Now Dirty Frag targets sk_buff frag members.
The naming convention references how these exploits manipulate kernel memory structures to corrupt read-only data. Copy Fail (CVE-2026-31431), disclosed April 29, fits the same vulnerability class even without “Dirty” branding. All involve page-cache corruption—a pattern that keeps producing critical exploits despite previous fixes.
Security researchers are likely searching for analogous bugs in other kernel subsystems. The ESP vulnerability sat undetected for nine years. The pattern suggests systemic issues with how the Linux kernel handles page-cache memory. Fixing one exploit doesn’t prevent similar vulnerabilities elsewhere. Expect more.
Key Takeaways
- Dirty Frag (CVE-2026-43284, CVE-2026-43500) allows any local user to gain root with a single command—active exploitation confirmed by Microsoft Security
- Second major Linux kernel privilege escalation in eight days (after Copy Fail on April 29)—pattern suggests deeper kernel security concerns
- Broken embargo left systems vulnerable with public exploit before patches were ready—AlmaLinux and Fedora patched within 24 hours, Ubuntu stable releases delayed
- Verify exposure with
lsmod | grep -E 'esp4|esp6|rxrpc'and patch immediately—waiting for next maintenance window is too slow - Assume breach: web shells, compromised SSH, and container escapes all provide sufficient local access for exploitation
The 24-48 hour emergency patch window isn’t paranoia. It’s the baseline response to a public exploit with confirmed active use.