On March 2-6, 2026, Bjarne Stroustrup—creator of C++—issued an unprecedented “call to urgent action” to the C++ standards committee (WG21), warning of “serious attacks on C++” from government safety mandates. The committee faces an impossible choice between two competing approaches to C++ memory safety: Profiles (Stroustrup’s gradual safety framework) versus Safe C++ (a Rust-like borrow checker, abandoned in September 2025 but still debated). Here’s the uncomfortable truth: both approaches fail. Profiles are too weak—optional, unenforced, with no implementation yet. Safe C++ was too radical—function coloring breaks compatibility. The real problem is that C++ waited 30 years to address memory safety seriously, and now faces retrofit solutions that satisfy nobody.
Stroustrup’s Unprecedented Warning – The Tipping Point
Bjarne Stroustrup’s paper P3651R0 (“Dealing with pointer errors: Note to the C++ standards committee members”), published March 6, 2026, warns WG21 of “unprecedented, serious attacks on C++” and urges the committee to “do something significant and be seen to do it.” He positions Profiles as “a framework that can do that” in response to government pressure. The note was written for WG21 members internally but was leaked to the web, triggering widespread discussion.
This is the first time in C++’s 40-year history that its creator has issued such an urgent warning. As The Register reported, Stroustrup’s call to action signals that external pressure—government mandates, industry migration to Rust—has reached a crisis level where the language’s future is genuinely at risk. Moreover, for 4.4 million C++ developers globally, this confirms that memory safety isn’t an academic debate anymore. It’s an existential threat.
Why Profiles Are Too Weak and Safe C++ Too Radical
The C++ committee is divided between two fundamentally incompatible solutions. Profiles (Stroustrup’s framework, P3081) offer gradual, opt-in safety rules enforced by compilers. However, they’re optional—developers can disable them. There’s no implementation yet; it’s still in proposal stage (R2 dated February 4, 2025). Regulators won’t accept “optional guidelines” as safety guarantees. This is the fatal flaw.
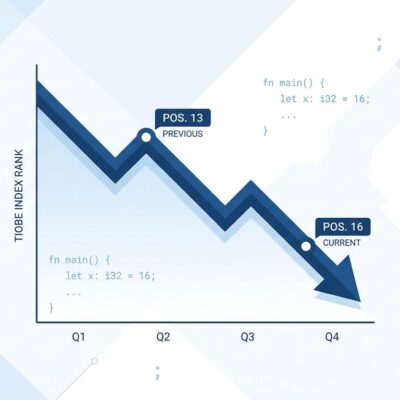
Safe C++—abandoned September 15, 2025—would have provided a Rust-like borrow checker with strict compile-time guarantees. Nevertheless, it introduced function coloring: safe functions can only call safe functions. Consequently, this makes gradual migration impossible. You can’t convert one module at a time; you must rewrite entire call chains at once. Sean Baxter, author of the Circle C++ compiler, confirmed: “Safe C++ is not being continued… The Rust safety model is unpopular with the committee… Profiles won the argument.” The WG21 vote split 30/45 for Profiles, 20/45 for Safe C++, with 6 neutral.
Neither approach works. Profiles can’t deliver the safety guarantees regulators demand—they’re optional and unenforced. Safe C++ can’t be adopted gradually—function coloring forces wholesale migration. The committee chose compatibility over safety, but that choice won’t satisfy CISA/FBI or convince developers to stick with C++ for new projects. Both camps lost.
Government and Industry Pressure Forces C++’s Hand
Government regulators and industry leaders are forcing action. CISA and the FBI’s October 2024 report declared C/C++ dangerous, setting a January 1, 2026 deadline for organizations to publish memory safety roadmaps. Specifically, the report states: “Not having a published memory safety roadmap by Jan. 1, 2026, is dangerous and significantly elevates risk to national security, national economic security, and national public health and safety.” The target: software supporting critical infrastructure. The recommended alternatives: Rust, Java, C#, Go, Python, Swift—anything memory-safe.
Microsoft escalated the pressure in December 2025 when distinguished engineer Galen Hunt announced: “My goal is to eliminate every line of C and C++ from Microsoft by 2030.” Furthermore, the company’s strategy: use AI to rewrite codebases at a rate of “1 engineer, 1 month, 1 million lines of code.” Hunt later clarified this was a research project, not a Windows rewrite. But the message was clear: even the largest C++ users are exploring exits.
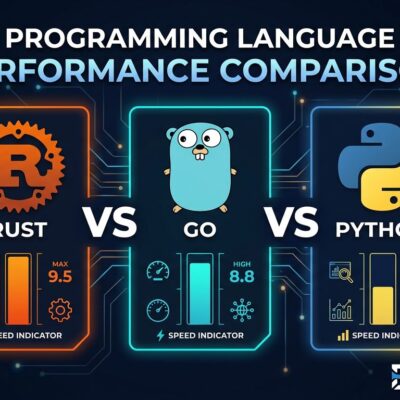
The numbers back this up. A 2026 Linux Foundation survey found 45% of new security-critical projects now use Rust. Meanwhile, 72% of embedded systems teams still rely on C++ for legacy integrations. The industry is bifurcating: memory-safe languages for new development, C++ for maintenance of existing code.
Why Both Approaches Fail – C++ Waited Too Long
The uncomfortable truth: C++ spent 30 years prioritizing performance over safety, and now both retrofit solutions are inadequate. Profiles won’t save C++ because they’re optional and unenforced. Developers can disable them. There’s no compiler implementation yet. Regulators demand guarantees, not guidelines. Saying “we have compiler flags” won’t satisfy CISA/FBI mandates for critical infrastructure.
Safe C++ couldn’t save C++ because function coloring makes gradual migration impossible. Entire call chains must be converted at once. The committee rejected it (30/45 vs 20/45 vote) precisely because it breaks compatibility—the one thing C++ has always preserved above all else. Copying Rust’s borrow checker doesn’t preserve C++’s identity as a flexible, backward-compatible language.
The real problem runs deeper. C++ had decades to address memory safety seriously but chose performance and backward compatibility instead. The State of C++ 2026 analysis makes this clear: the language now faces a forced choice between adopting half-measures (Profiles) that don’t satisfy regulators, copying Rust (Safe C++) and losing compatibility advantages, or dying slowly via regulation and industry migration to memory-safe alternatives. None of these options are good.
For new projects, Rust already won. It’s not a future possibility—it’s the present reality. The 45% adoption rate for security-critical projects proves it. C++’s future is legacy maintenance, not greenfield development. That’s not death, but it’s a massive shift from C++’s historical dominance in systems programming.
What Developers Should Actually Do
For new projects, default to memory-safe languages—Rust, Go, Swift—unless C++ is required for specific reasons (performance-critical domains like gaming, legacy integration constraints, embedded systems without Rust toolchains). If choosing C++, plan for Profiles adoption when C++26 arrives, though implementation timeline remains uncertain. Document safety requirements early in project planning to avoid surprises when CISA/FBI-style mandates arrive.
For existing C++ codebases, publish a memory safety roadmap by January 1, 2026. While CISA/FBI guidance isn’t a legal mandate, it’s strong enough that organizations in critical infrastructure can’t ignore it. Prioritize network-facing code and cryptography for migration or safety measures. Evaluate hybrid approaches: Rust for new components, C++ with Profiles for existing code, FFI (Foreign Function Interface) for interop between the two.
For individual developers, learn Rust alongside C++. Both skills are valuable: Rust for new projects, C++ for maintaining the billions of lines of legacy code at Microsoft, Google, Meta, Amazon, and thousands of other companies. C++ expertise remains valuable for decades—legacy code doesn’t disappear overnight. But the growth is in memory-safe languages. Developers who understand both worlds have the strongest career prospects.
Key Takeaways
- Stroustrup’s March 2-6, 2026 “call to urgent action” is the first such warning in C++’s 40-year history, signaling the existential threat from government mandates and industry Rust migration
- Profiles are too weak—optional, unenforced, no implementation yet—while Safe C++ was too radical, with function coloring breaking compatibility and forcing wholesale migration
- CISA/FBI set a January 1, 2026 deadline for memory safety roadmaps, Microsoft announced a 2030 “eliminate C++” goal (later clarified as research), and 45% of new security-critical projects now use Rust
- For new projects, Rust is the default. For existing C++ codebases, hybrid approaches are realistic: Rust for new features, C++ with Profiles for legacy, FFI for interop
- C++ expertise remains valuable for decades of legacy maintenance, but the growth is in memory-safe languages. Both skills matter in 2026’s hybrid development landscape