NIST just made AI agents a government priority. If you’re building them, Q4 2026 just became your deadline.
The National Institute of Standards and Technology launched the AI Agent Standards Initiative on February 17, 2026, targeting the security and interoperability gaps plaguing autonomous AI deployment. The timing isn’t coincidental: 88% of organizations reported AI agent security incidents in the past year, yet only 14.4% send agents to production with proper security approval. NIST’s shift from experimental tolerance to standardization signals the industry moving from “move fast” to “move right.”
The Q4 2026 AI Agent Interoperability Profile and forthcoming SP 800-53 control overlays will define how enterprises deploy AI agents securely. If you’re architecting AI systems now, these standards should inform your decisions today, not later.
Three Pillars Building on Proven Protocols
NIST isn’t starting from scratch. The initiative operates on three strategic pillars, built atop existing protocols that already work.
First, industry-led standards facilitation through technical convenings and gap analyses. Second, community-driven open-source protocols, with the Model Context Protocol (MCP) and Agent-to-Agent (A2A) protocol identified as interoperability baselines. Third, fundamental research on agent authentication, identity infrastructure, and security evaluations.
Here’s what matters: MCP already hit 97 million monthly SDK downloads by March 2026, up from 2 million when Anthropic launched it in November 2024. It’s the de facto standard for how agents connect to tools, databases, and services. Google’s A2A protocol, now managed by the Linux Foundation, handles agent-to-agent communication with backing from Atlassian, Salesforce, SAP, ServiceNow, and 50+ other major players.
The interoperability stack is actually two layers: MCP for agent-to-tool communication, A2A for agent-to-agent coordination, and NIST standards adding security, identity, and enterprise controls on top. If you’re building AI agents, learn MCP and A2A now. NIST isn’t reinventing these—they’re standardizing security around them.
The Q4 2026 Deadline You Should Care About
NIST’s timeline creates a clear inflection point. April 2026 brings sector-specific listening sessions for healthcare, finance, and education. Q4 2026 delivers the AI Agent Interoperability Profile. Then come SP 800-53 control overlays for agentic systems.
That Q4 publication becomes the authoritative reference for enterprise deployment. SP 800-53 overlays will define compliance for federal systems and likely shape private sector standards. Architecture decisions made between now and June either align with or clash with these standards. Early alignment means competitive advantage. Late retrofitting means technical debt.
This follows NIST’s playbook from the Cybersecurity Framework in 2014, which became industry standard within two years and reshaped how organizations approached security across sectors.
The Security Crisis Driving Standards Now
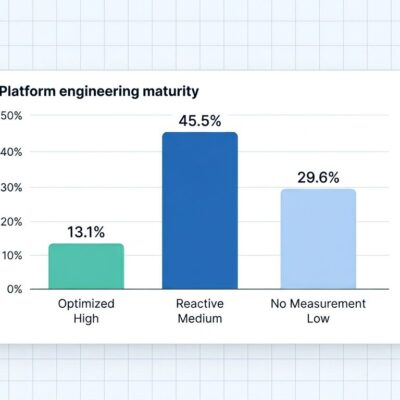
Enterprise AI agent security is broken, and the numbers prove it.
Eighty-eight percent of organizations reported AI agent security incidents in the past year. Only 14.4% send agents to production with full security approval. Yet 82% of executives think their policies work—a confidence-reality gap that’s costing organizations real money. Just 24.4% have visibility into agent-to-agent communications, according to Gravitee’s 2026 survey.
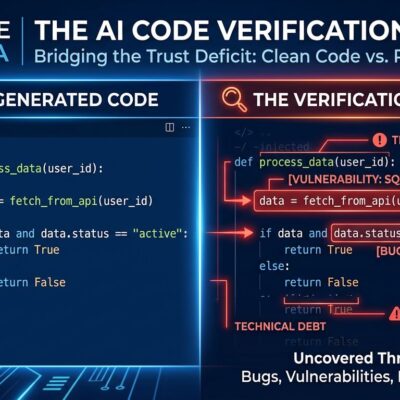
Shadow AI is rampant: agents deployed by engineering teams without security review, connecting to MCP servers and external APIs never mapped or approved. The execution layer—where agents invoke tools—is the new attack surface. MCP server vulnerabilities, prompt injection attacks, and data exfiltration through AI assistants represent the expanding threat landscape.
Organizations are responding with AI agent gateways that sit between agents and tools, intercepting invocation requests to evaluate against policy before approving or blocking in real-time. Don’t wait for NIST standards to address security. The 14.4% getting security approval now are ahead. The 88% experiencing incidents are paying the price.
What This Means for Developers
NIST isn’t creating new interoperability protocols or mandating implementations. This is voluntary guidance building on industry direction—but voluntary NIST standards historically become industry defaults, especially for enterprises and government contractors.
Think of it as paving the cowpaths: NIST standardizes what the industry already does (MCP and A2A adoption) while filling security gaps.
Enterprise developers building production AI agent systems should act now. Learn MCP at modelcontextprotocol.io and understand A2A at a2a-protocol.org. Follow the NIST AI Agent Standards Initiative. Design agent architectures with security gates instead of waiting for standards.
The shift is clear: from experimental AI agents to production-ready systems, from “build fast and iterate” to “build with standards in mind,” from siloed agents to interoperable ecosystems. Q4 2026 marks when autonomous AI gets real. Your architecture decisions today determine whether you’re ready.