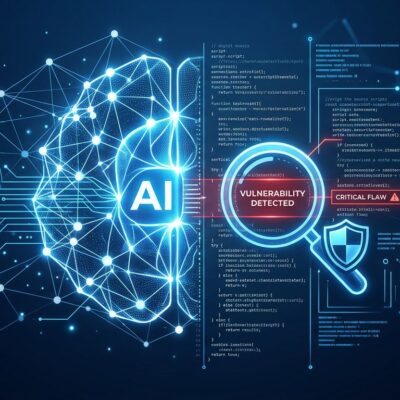
Eighty-five percent of major enterprises are experimenting with AI agents, but only 5% have moved them into production. That’s not a technology problem—it’s a trust problem. At RSA Conference 2026 on April 1, Cisco unveiled the first comprehensive Zero Trust architecture specifically designed for autonomous AI agents, directly addressing the security gap that’s keeping most agent deployments stuck in pilot purgatory.
The blocker isn’t capability. It’s the permission paradox that traditional security can’t solve.
The Permission Paradox
An autonomous agent executing a multi-step task might hit 40 different APIs in under a minute, spawn sub-agents, and access databases it’s never touched before. All autonomously. Traditional role-based access control was designed for predictable human behavior, not machines making real-time decisions.
This creates an impossible choice: over-provision permissions and create security holes, or under-provision and render agents useless for unpredictable tasks. There’s no middle ground.
The data backs this up. Forty-five percent of technical teams use shared API keys for agent-to-agent authentication—a security nightmare where attribution becomes impossible. Eighty-eight percent of organizations reported confirmed or suspected AI agent security incidents in the last year. Nearly half of cybersecurity professionals now call agentic AI the top attack vector for 2026.
Take a deployment agent that normally accesses code repositories and triggers CI/CD pipelines. Traditional security would validate its credentials and allow access. But what happens when it suddenly starts reading customer PII from a database it’s never accessed? The agent technically has the credentials, but the behavior is anomalous. Role-based access control can’t catch that.
Cisco’s Three-Pillar Solution
Cisco’s architecture addresses agent security across three dimensions: protecting the world FROM agents, protecting agents FROM manipulation, and detecting incidents at machine speed.
The first pillar establishes individual identity for each agent through Duo IAM—no more shared service accounts. Every agent gets registered with unique credentials, and all tool traffic routes through an MCP Gateway that enforces access policies. If that deployment agent tries to access customer data, behavioral anomaly detection flags the deviation from its established baseline.
The second pillar hardens agents before deployment. AI Defense Explorer Edition provides self-service red teaming. DefenseClaw, an open-source framework Cisco launched on GitHub March 27, scans every skill, tool, and plugin before admission to the agent environment. At runtime, it inspects every message flowing in and out. Integration with NVIDIA OpenShell adds OS-level isolation using Linux namespaces, Landlock, and seccomp.
The third pillar operates at machine speed. Splunk Enterprise Security enhancements introduce six specialized AI agents for security operations: Detection Builder, Triage, Malware Threat Reversing, Guided Response, Standard Operating Procedure, and Automation Builder. Agents protecting against agents—fighting fire with fire.
Most importantly, this isn’t vaporware. Detection Studio and Malware Threat Reversing are generally available now. The remaining features launch between April and June 2026.
The MCP Infrastructure Layer
Model Context Protocol has become the universal plumbing of agentic AI. Over 10,000 published MCP servers connect agents to external systems across Claude, Cursor, Microsoft Copilot, Gemini, and ChatGPT. It’s rapidly becoming the HTTP of AI agents.
But MCP prioritized ease of adoption over security. Studies find OAuth flaws, command injection vulnerabilities, unrestricted network access, and plaintext credentials in open MCP servers. The Coalition for Secure AI identified 12 core threat categories spanning nearly 40 distinct threats specific to MCP deployments.
Cisco’s MCP Gateway provides centralized policy enforcement at the protocol level. Every request becomes traceable across the entire execution path—from end user through intermediate MCP servers to the final action. This isn’t endpoint security. This is securing the infrastructure layer most developers don’t think about.
Agent Security as a Distinct Discipline
The security industry spent 15 years building Zero Trust for humans. Cisco’s announcement validates that the entire model needs rethinking from first principles for autonomous agents.
This isn’t bolting AI features onto existing security products. It’s recognizing that agents making real-time decisions, spawning sub-agents (25.5% of deployed agents have this capability), and creating unpredictable access patterns require fundamentally different architecture. The federal government issued a Request for Information on agent security considerations in January 2026. Bessemer Venture Partners called it “the defining cybersecurity challenge of 2026.”
The industry is taking notice. Despite 80.9% of technical teams being in active testing or production with agents, only 14.4% have full security and IT approval. That gap reveals the disconnect between deployment speed and security readiness.
What This Means for Production Deployment
For the 85% of enterprises stuck in experimentation, Cisco’s architecture provides a roadmap out of pilot purgatory.
Start with discovery. Cisco Identity Intelligence finds shadow AI deployments—agents launched by engineering teams without security review that connect to unmapped tools and external APIs. Get visibility into what’s actually running.
Establish individual identities for each agent through Duo IAM. No shared credentials. Implement behavioral baselines so anomalies get flagged, not just credential validation. If you’re building custom agents, use DefenseClaw for pre-deployment scanning. It’s open source and available now.
The practical actions are straightforward: audit current agent permissions (most are over-provisioned for convenience), implement granular logging at the request level, and make agent identity foundational to your architecture, not an afterthought.
Closing the Gap
The 85% to 5% production gap isn’t about agent capability. It’s about trust. Enterprises know their agents work in the lab. They don’t trust them in production because traditional security models fundamentally fail for autonomous systems.
Cisco’s Zero Trust architecture addresses the root cause. Whether it closes the gap remains to be seen—the products just launched. But for the first time, enterprises have a comprehensive framework purpose-built for agent security, not retrofitted from human-centric models.
Trust unlocks production deployment. The tooling to build that trust is available now.