On May 11, Google’s Threat Intelligence Group disclosed the first confirmed case of hackers using artificial intelligence to discover and weaponize a zero-day vulnerability. The attackers developed a working exploit to bypass two-factor authentication on a widely-used web administration tool, planning a “mass exploitation event” that Google intercepted and likely prevented. What was once theoretical—AI-powered offensive hacking—is now operational reality.
The timeline for cyberattacks has fundamentally changed. Traditional vulnerability discovery and exploit development took weeks or months. With AI assistance, that process now happens in hours or days.
How Google Detected AI-Generated Exploit Code
Google’s forensic analysis revealed telltale signs of AI-generated code. The Python exploit contained detailed docstrings explaining each function—unusual for criminal malware. More revealing: the code included a “hallucinated” CVSS vulnerability score that the AI model simply invented and embedded in comments. Human hackers don’t document their exploits like tutorials or make up fake severity ratings.
According to Google’s official report, “The script contains an abundance of educational docstrings, including a hallucinated CVSS score, and uses a structured, textbook Pythonic format highly characteristic of LLM training data.” The exploit worked—it successfully bypassed two-factor authentication—but looked like something generated for a coding class, not a criminal operation.
This is concrete proof, not speculation. Security teams now know what AI-generated exploits look like and can potentially detect them. More importantly, it confirms that AI models are being actively used for offensive hacking in the wild, not just in research labs.
The Anthropic Mythos Connection
Google’s discovery validates warnings issued one month earlier. On April 7, Anthropic announced Claude Mythos Preview, an AI model so capable at finding vulnerabilities that it identified thousands of zero-days in every major operating system and web browser. The model’s power was alarming enough that Anthropic restricted access to roughly 50 trusted organizations and launched Project Glasswing—a $100 million initiative to use AI to secure critical software before making such capabilities widely available.
Project Glasswing’s partners include Apple, Amazon, Google, Microsoft, JPMorgan Chase, and the Linux Foundation, plus over 40 additional organizations. The strategy: use Mythos to find bugs before attackers do, patch proactively, and build AI-powered defensive tools. Anthropic committed $100 million in usage credits and $4 million in direct donations to open-source security organizations.
The fact that a criminal group already has access to similar AI capabilities—whether through Mythos, another model, or clever orchestration of public models—shows the threat is immediate. As CNBC reported on May 8, “Anthropic’s powerful new Mythos AI model pushed concerns about AI’s impact on cybersecurity to a tipping point.”
AI Compresses Vulnerability Timelines
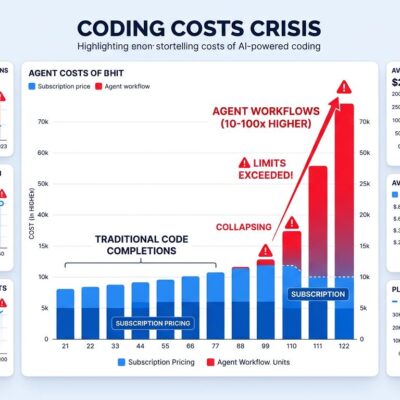
AI collapses the vulnerability lifecycle. Traditional exploitation required weeks of manual code analysis to find bugs, then days to weeks to develop working exploits. AI scans codebases, identifies vulnerabilities, and generates exploit code in a fraction of that time—potentially within a single day from discovery to weaponization.
According to watchTowr’s Head of Threat Intelligence, “AI is already accelerating vulnerability discovery, reducing the effort needed to identify, validate, and weaponize flaws. Discovery, weaponization, and exploitation are faster. Timelines have been compressing for years.”
Google’s assessment is stark: “For every zero-day traced back to AI, there are probably many more out there.” State-sponsored actors from China and North Korea are actively experimenting with AI for vulnerability discovery, “persona-driven jailbreaking” of AI safety guardrails, and bulk exploit validation.
What Defenders Must Do Now
The security community is divided on whether this represents a tipping point or incremental change. Some experts view this as the moment AI fundamentally altered cybersecurity. Others argue that skilled hackers could already do this work—AI merely accelerates existing capabilities. Both perspectives have merit.
However, whether this shift is “revolutionary” or “evolutionary,” the practical impact is identical: defenders must adapt to faster attack cycles. Traditional security response times are obsolete. If attackers can discover and weaponize vulnerabilities in hours, monthly “Patch Tuesday” cycles are dangerously slow. Organizations need continuous patching and AI-powered proactive scanning to stay ahead.
The response is already underway. Banks are slashing patch times in response to the Mythos announcement. Japan’s Prime Minister ordered a comprehensive cybersecurity review specifically citing AI-enabled threats. Project Glasswing demonstrates how the industry is fighting back—using the same AI capabilities to find and fix vulnerabilities before attackers can exploit them.
The AI security arms race isn’t coming. It’s here.