LinkedIn secretly scans your computer for over 6,000 software products every time you visit linkedin.com—without consent, notification, or disclosure in its privacy policy. Privacy researchers at browsergate.eu exposed the operation in March 2026, revealing hidden JavaScript code that probes browsers for installed extensions, collects sensitive data including religious beliefs, political opinions, disabilities, and job search activity, and transmits results to LinkedIn’s servers and third-party companies. The practice affects all 1 billion LinkedIn users who use Chrome-based browsers and violates GDPR by processing special category data without legal basis.
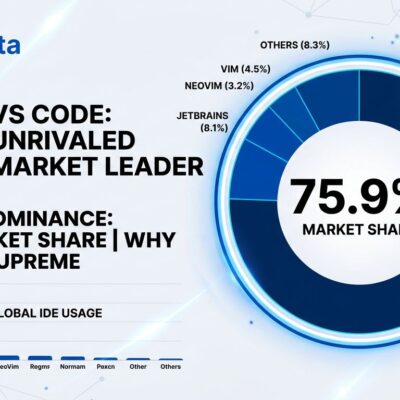
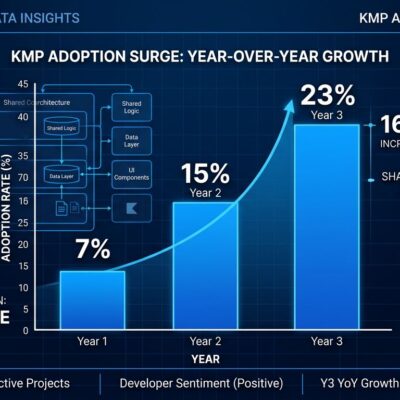
The scale alone is staggering. LinkedIn’s scan list exploded 1,252% from 461 products in 2024 to 6,222 in February 2026. Between December 2025 and February 2026, LinkedIn added 708 new extensions to its scan list—roughly 12 extensions per day. At this growth rate, LinkedIn could be scanning 10,000+ products by year’s end.
From 461 to 6,222 Products: Surveillance at Industrial Scale
The BrowserGate investigation reveals exactly what LinkedIn is tracking. The 6,222 scanned extensions fall into categories that reveal far more than software preferences: 509 job search tools (Indeed, Glassdoor, Monster extensions), 200+ LinkedIn competitor products (Apollo, Lusha, ZoomInfo, Hunter.io), religious markers (Muslim prayer extensions), political indicators (news source selectors, fact-checkers), and disability tools (ADHD managers, autism support, screen readers).
This isn’t static surveillance—it’s aggressively expanding. The 12-per-day addition rate shows LinkedIn is systematically categorizing every extension that reveals user identity, behavior, or commercial intent. The scanned extensions have a combined user base of 405 million people. BrowserGate maintains a searchable database where users can check if their extensions are being tracked.
Special Category Data: Religion, Politics, Disabilities Exposed
Here’s where LinkedIn crosses from privacy violation into illegal territory. Under GDPR Article 9, processing special category data—religious beliefs, political opinions, disabilities—requires explicit consent. LinkedIn collects all three without asking.
BrowserGate researchers found LinkedIn scans for extensions identifying practicing Muslims, political orientation indicators (liberal vs conservative news sources), and tools built specifically for neurodivergent users. Worse, LinkedIn scans for 509 job search tools, revealing who’s secretly job hunting. Because LinkedIn knows each user’s employer from their profile, they can identify “Employee X at Company Y is using Glassdoor extension”—a massive conflict of interest if LinkedIn alerts employers or targets recruitment ads.
This creates chilling effects. Developers who install prayer time extensions don’t expect LinkedIn to catalog their religious identity. Political indicators enable discriminatory targeting. Disability data exposure violates medical privacy norms. LinkedIn is weaponizing personal data against users’ interests.
Corporate Espionage: Extracting Competitor Customer Lists
LinkedIn scans for over 200 products that directly compete with its own sales tools like Sales Navigator. By detecting competitor extensions (Apollo, Lusha, ZoomInfo) and cross-referencing with user employers, LinkedIn extracts customer lists from thousands of software companies without anyone knowing.
The mechanics are simple: LinkedIn detects “User has Apollo extension installed” + “User works at Company X” = “Company X uses Apollo for sales intelligence.” Multiply this across millions of users and LinkedIn builds a comprehensive competitive intelligence database showing exactly who uses which tools, how many seats, what roles. Competitors spend millions building customer bases—LinkedIn steals that intelligence by scanning users’ browsers.
This is industrial espionage disguised as website functionality. It potentially violates EU competition law (abuse of dominant position as designated gatekeeper) and corporate confidentiality. LinkedIn users become unwitting intelligence sources against the tools they choose to use.
GDPR Violations: No Consent, $8 Billion in Potential Fines
LinkedIn’s privacy policy contains zero mentions of browser extension scanning. BrowserGate researchers searched for keywords like “extension”, “browser”, “installed”, “software”, “scan”, “detect”, “fingerprint”—nothing. The practice is completely undisclosed.
Under GDPR Article 9, explicit consent is required before processing special category data. LinkedIn has no consent mechanism. Users are never asked, never told. This is an unambiguous violation with penalties up to 4% of global revenue—roughly $8 billion for Microsoft. If Digital Markets Act violations are confirmed (LinkedIn is a designated gatekeeper), fines escalate to 10% of worldwide turnover, or approximately $20 billion.
Legal action has already begun. Estonian company Teamfluence Signal Systems OÜ filed a preliminary injunction at Munich Regional Court in January 2026 (Case No. 37 O 104/26), alleging Digital Markets Act violations, EU competition law breaches, and German data protection rule violations.
How to Protect Yourself
BrowserGate currently only affects Chrome-based browsers (Chrome, Edge, Brave on Chromium). Firefox and Safari are not affected—yet. Developers have several protection options.
The simplest defense: use Firefox or Safari for LinkedIn. The scanning method relies on Chrome extension detection, which doesn’t work in Firefox’s architecture. Alternatively, create a LinkedIn-only Chrome profile with zero extensions installed—browser isolation breaks the surveillance. Privacy-focused browsers like Brave with fingerprinting protection enabled also block the detection mechanism.
EU users have legal recourse. File GDPR complaints with your national data protection authority. Enough complaints trigger regulatory investigations and force enforcement action. LinkedIn bet users wouldn’t notice or care—prove them wrong.
Key Takeaways
- LinkedIn scans 6,222 browser extensions (up 1,252% from 461 in 2024), adding 12 new extensions daily, affecting all 1 billion users on Chrome-based browsers
- The scanning reveals special category data protected under GDPR Article 9: religious beliefs, political opinions, disabilities, and job search activity—all without consent or disclosure
- LinkedIn extracts competitor customer lists by scanning 200+ sales intelligence tools (Apollo, Lusha, ZoomInfo) and cross-referencing with user employers—industrial espionage at scale
- Legal violations are clear: no consent for special category data, zero privacy policy disclosure, and Munich court case filed alleging GDPR, Digital Markets Act, and competition law breaches
- Protect yourself: switch to Firefox or Safari for LinkedIn, use browser isolation (LinkedIn-only profile with zero extensions), or file GDPR complaints with data protection authorities
LinkedIn has betrayed the trust developers place in it as a professional networking platform. The company isn’t just violating privacy law—it’s running a surveillance operation that profiles users by religion and politics, identifies job seekers to exploit commercially, and steals competitive intelligence from software companies. At minimum, switch browsers. Better yet, delete your LinkedIn account or demand regulatory action. Microsoft needs to feel consequences for turning a professional network into an industrial-scale spying machine.