LinkedIn is running a covert browser fingerprinting operation that scans for 6,278 specific browser extensions and collects 48 device data points on every visitor—without disclosure in its privacy policy. The practice, dubbed “BrowserGate” by European researchers who exposed it this week, injects a 2.7MB JavaScript bundle called “Spectroscopy” that silently probes your browser, encrypts the fingerprint with RSA encryption, and injects it as an HTTP header into every API request you make on the platform.
The story broke when Fairlinked e.V., a European association of LinkedIn users, reverse-engineered the platform’s production JavaScript and found what they’re calling “one of the largest undisclosed data collection operations in the history of the commercial internet.” The discovery gained traction on Hacker News yesterday (309 points, 118 comments) and was covered by major tech outlets including BleepingComputer, Tom’s Hardware, and The Next Web.
How LinkedIn’s ‘Spectroscopy’ Script Works
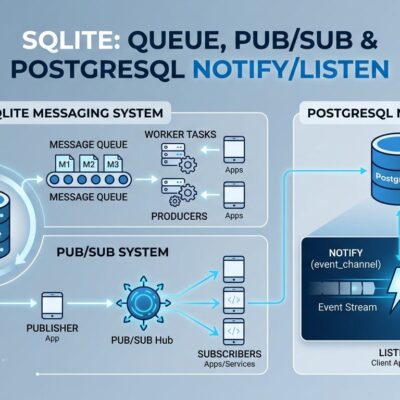
LinkedIn’s fingerprinting system is sophisticated and designed specifically to avoid detection. The script fires 6,222 simultaneous requests probing for browser extension IDs by attempting to access chrome-extension://[ID] resources. When Chrome extensions inject content into web pages, they leave traces with the chrome-extension:// URL scheme. Spectroscopy recursively inspects every DOM node, checking text and element attributes for these references, then extracts the 32-character extension ID when found.
Beyond extensions, the script collects 48 device characteristics: CPU core count, available memory, screen resolution, timezone, language settings, battery status, audio hardware, and storage capacity. This data is combined with extension IDs, serialized to JSON, encrypted with RSA (LinkedIn’s key identifier: “apfcDfPK”), and transmitted to telemetry endpoints at /li/track and /platform-telemetry/li/apfcDf.
The stealth design is deliberate. Moreover, the script uses requestIdleCallback for idle execution (no visible performance impact), staggered probing to distribute requests over time, a hidden 0×0px iframe for third-party integration, and silent error handling with empty catch blocks that log nothing to the console. Additionally, the RSA encryption makes the payload unreadable even in network inspectors.
Furthermore, LinkedIn’s extension list has grown aggressively: 2,000 extensions in 2025, 3,000 in February 2026, and now 6,278 as of April 2026—a 214% increase in 18 months. The fingerprint is permanently injected as an HTTP header into every subsequent API request during the session, and shared with HUMAN Security, an American-Israeli cybersecurity firm.
What LinkedIn Is Really Looking For
The 6,278 extension list reveals scope that goes far beyond anti-scraping security. LinkedIn scans for 200+ competitive sales tools including Apollo, Lusha, and ZoomInfo. Because LinkedIn knows your employer from your profile, detecting competitor tool usage reveals which companies are evaluating rival products—classic corporate espionage.
Worse, the list includes 509 job search extensions. Think about that: LinkedIn is scanning to see if you’re secretly job hunting on the very professional network where your current employer can see your profile. The privacy implications are staggering.
Additionally, the list includes extensions identifying religious practices (tools for practicing Muslims), political orientation, and neurodivergent users (ADHD/autism productivity tools). Combined with LinkedIn’s knowledge of your real name, employer, and job title, these extensions enable sensitive inferences that go far beyond what’s disclosed in the privacy policy.
LinkedIn’s Defense vs Privacy Critics
LinkedIn claims the scanning is a security measure to detect extensions that scrape data or violate Terms of Service. Their official response to BleepingComputer: “To protect the privacy of our members, their data, and to ensure site stability, we do look for extensions that scrape data without members’ consent or otherwise violate LinkedIn’s Terms of Service.”
However, critics aren’t buying it. Fairlinked e.V. notes the practice is completely undisclosed: “Every time you open LinkedIn in a Chrome-based browser, hidden code runs on your device. You were never asked. You were never told. And none of it appears in LinkedIn’s privacy policy.”
The justification doesn’t match the scope. If this is about anti-scraping, why scan job search tools and religious extensions? Why track 200+ competitor products? And why design the system specifically to avoid detection with stealth techniques like RSA encryption and silent error handling?
Legal experts note potential GDPR violations. Scanning thousands of extensions may constitute processing of special-category personal data, and the lack of user awareness likely invalidates any implied consent. The Irish Data Protection Commission—which has already shown willingness to challenge tech giants—may investigate.
How to Protect Your Privacy
The best defense is switching to Firefox, which randomizes extension resource URLs so LinkedIn can’t probe for known IDs. This blocks the extension detection technique entirely.
Alternative protections: use Brave with fingerprint protection enabled, or Safari 26 which has Advanced Fingerprinting Protection (AFP) that injects noise into fingerprint data. Chrome offers no default protection—you’ll need extensions like uBlock Origin, though Manifest V3 has weakened these tools.
Developers should audit their installed extensions. Every extension increases your fingerprint surface area. Remove anything you don’t actively use weekly. Consider using different browsers for different activities to compartmentalize tracking.
The Post-Cookie Surveillance Era
BrowserGate signals a broader trend: as third-party cookies die, fingerprinting becomes the new surveillance frontier. LinkedIn was caught because researchers reverse-engineered the JavaScript, but the practice may be widespread and undisclosed across other platforms.
Browser vendors are fighting back. Chrome 142 Canary is testing canvas fingerprinting blocks in Incognito mode. Safari 26 enabled AFP across all browsing modes. Firefox has randomized extension URLs for years. However, LinkedIn’s 214% growth in tracked extensions (2,000 → 6,278 in 18 months) shows the arms race is escalating.
The question developers should ask: what other platforms are doing this without disclosure?