Rust has crossed the inflection point from experimental to production-critical in 2026. Major enterprises—Meta’s WhatsApp, Google’s Android, and the Linux kernel—have moved beyond pilot programs to billion-user deployments, with 82% of developers reporting improved performance and reliability. The Linux kernel officially declared Rust “no longer experimental” in December 2025, while WhatsApp replaced 160,000 lines of C++ with 90,000 lines of memory-safe Rust code protecting 3 billion users. The question for systems programmers has shifted from “Should we use Rust?” to “What reason do we have NOT to use Rust?”
Memory safety vulnerabilities account for 70% of security issues in C/C++ codebases, costing enterprises billions in breaches and remediation. Rust eliminates these entire classes of bugs at compile time, not runtime—offering the performance of C++ with safety guarantees, without garbage collection overhead.
Billion-User Production Deployments Prove Rust’s Readiness
Three major production deployments demonstrate Rust’s transition from experiment to critical infrastructure. WhatsApp (Meta) rewrote its media handling library from 160,000 lines of C++ to 90,000 lines of Rust, deployed to 3 billion devices across Android, iOS, Mac, Web, and Wearables. Moreover, the Rust version showed performance and runtime memory usage advantages over C++ while eliminating 44% of the code.
Meta Engineering was direct about the motivation: “The majority of high severity vulnerabilities published were due to memory safety issues in code written in C and C++. This isn’t just a rewrite; it’s a structural shift that eliminates entire classes of bugs before the code ever runs.” That’s not incremental improvement—it’s eliminating buffer overflows and use-after-free vulnerabilities that previously drove exploits and spyware.
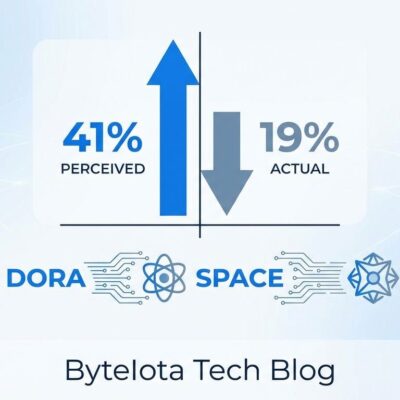
Google’s Android replaced critical C/C++ components—PNG parsers, JSON parsers, web fonts—with Rust in the Android Open Source Project (AOSP). The result: memory safety vulnerabilities dropped below 20% for the first time in Android’s history, representing a 1,000x reduction in vulnerability density. Android 16 devices now ship with an ashmem (anonymous shared memory) memory allocator built in Rust, meaning millions of consumer devices run Rust in production daily.
The Linux kernel delivered the most significant credibility boost. In December 2025, kernel maintainers declared Rust “no longer experimental” and “a core part of the kernel.” By early 2026, over 600,000 lines of production Rust code exist across drivers, filesystem abstractions, and core subsystem bindings. Greg Kroah-Hartman called Linux 6.13 “the tipping point” for Rust driver development, with Rust-based drivers proving safer than C equivalents. Dave Airlie, the DRM maintainer, stated the DRM project is about a year away from requiring Rust and disallowing C for new drivers.
How Rust Eliminates Memory Bugs at Compile Time
Rust’s ownership model catches 83% of memory errors before code runs through three compiler-enforced rules: every value has exactly one owner, you can have either one mutable reference OR any number of immutable references (but not both), and memory is automatically freed when the owner goes out of scope. The borrow checker enforces these rules at compile time. Consequently, if your program compiles, you’ve already eliminated use-after-free, double-free, and data races.
Compare the same memory bug in C++ versus Rust:
C++ (Vulnerable):
char* buffer = malloc(100);
free(buffer);
printf("%s", buffer); // Use-after-free: undefined behavior, potential exploitRust (Compile-Time Error):
let buffer = String::from("data");
drop(buffer);
println!("{}", buffer); // ERROR: "value borrowed here after move"The Rust compiler refuses to build code with memory safety violations. Furthermore, this is fundamentally different from runtime safety checks (which have performance overhead) or garbage collection (which has unpredictable pauses). Rust’s zero-cost abstractions mean safety checks compile away—the borrow checker operates at compile time, not runtime. For more details, see the official Rust book’s explanation of ownership.
Rust Matches C++ Performance Without the Memory Bugs
The “Rust is slower than C++” argument collapsed under production evidence. While C++ edges Rust by 5-10% in controlled microbenchmarks (matrix multiplication, file I/O), those gains disappear in real-world workloads. Additionally, WhatsApp’s Rust rewrite showed “performance and runtime memory usage advantages over the C++” version despite eliminating 44% of the code.
Bloomberg’s 2026 Performance Benchmark Report found C++ runs 15-20% faster only in ultra-latency-critical high-frequency trading, where microseconds matter more than safety. For general-purpose high-performance applications, Rust and C++ are highly competitive—the choice depends more on safety requirements than raw performance. Real-world applications like PNG decoding, merge sort, and concurrent operations show Rust at parity or ahead of C++.
Rust’s zero-cost abstractions deliver on the promise: you’re not trading performance for safety. You’re getting both.
The Learning Curve: Front-Loaded Pain for Long-Term Gain
Be honest with engineering teams: Rust isn’t a “learn over the weekend” language. Developers need 2-3 months to reach productivity, compared to 1-2 weeks for Go. However, the steepest climb comes in the first 1-2 months, with borrow checking and ownership as the primary pain points. According to official Rust community research, “basically every beginner struggles with” the borrow checker.
Nevertheless, Rust experts report borrow checker concerns “go away with experience”—it’s a challenge that fades, not a permanent limitation. The learning curve is front-loaded pain for long-term gain. Once developers internalize ownership patterns, production debugging time drops significantly because memory bugs are eliminated at compile time. The 82% of developers reporting improved performance and reliability didn’t get there instantly—they invested the learning time upfront.
When NOT to Use Rust: The Honest Assessment
Rust excels at systems programming and security-critical applications, but it’s not universally appropriate. Skip Rust for small scripting tasks (file automation, DevOps scripts)—Python or shell scripts are faster to write and maintain. Avoid Rust for rapid prototyping where you’re still discovering functionality and making frequent architectural changes. Developer feedback is consistent: “Rust limits speed of prototyping due to strict borrow semantics. Small tweaks, such as what component owns a piece of data, propagate across the entire system.”
GUI-heavy applications remain a weak spot for Rust. The ecosystem is less mature than C++ with Qt or web technologies, and iteration speed suffers. Dynamic languages like Python or JavaScript are better choices when you need to iterate quickly without fighting the compiler.
Use Rust when:
- Systems programming (operating systems, device drivers, embedded systems)
- High-performance services (networking, media processing, game engines)
- Security-critical applications (cryptography, authentication, sandboxing)
- Replacing C/C++ where memory bugs are causing production incidents
Don’t use Rust when:
- Scripting and automation (Python wins on development speed)
- Rapid prototyping with frequent architectural changes (Go or Python wins)
- GUI-heavy applications (less mature ecosystem, slower iteration)
- Teams can’t dedicate 2-3 months for developers to reach productivity
Knowing when NOT to use Rust is as important as knowing when to use it. Teams that try to use Rust for rapid prototyping or scripting will have a bad experience and blame the language, when the real issue is using the wrong tool for the job.
Is Rust Worth It in 2026?
Rust’s 2026 inflection point isn’t hype—it’s billion-user production reality backed by hard data:
- For systems programming and security-critical applications: Yes, unequivocally. The Linux kernel, WhatsApp, and Android deployments prove Rust is production-ready at massive scale.
- For high-performance services: Yes, if memory safety matters. Rust matches C++ performance while eliminating 70% of typical security vulnerabilities.
- Budget the learning curve: 2-3 months to productivity. The investment pays off in reduced production bugs and debugging time.
- Not for everything: Skip Rust for scripting, rapid prototyping, and GUI-heavy applications where iteration speed matters more than memory safety.
- Start small: Rewrite a self-contained C++ library, measure the impact on bug rates and performance, then scale adoption based on results.
The question has shifted from “Is Rust ready?” to “What’s your reason for staying with C++?” For new systems-level projects in 2026, Rust has become the default choice backed by enterprise evidence, not developer enthusiasm. The proof is in production: 3 billion WhatsApp users, millions of Android devices, and the Linux kernel itself.