The European Commission confirmed last week that hackers stole over 350GB of sensitive data from its AWS cloud infrastructure. The breach, detected March 24 and claimed by the ShinyHunters extortion group on March 26, exposed mail servers, databases, confidential documents, and contracts. The irony: This is the same regulatory body that has issued €7.1 billion in GDPR fines to companies for inadequate data protection since 2018. Turns out the organization writing and enforcing Europe’s data security rules can’t secure its own AWS accounts.
The GDPR Enforcer Gets Breached
The European Commission isn’t new to handing out penalties. In 2025 alone, it issued €1.2 billion in GDPR fines, including a €530 million penalty against TikTok for unlawful international data transfers. European data breach notifications hit a record 443 per day in 2025, up 22% year-over-year. The Commission built an entire regulatory apparatus around data protection compliance. Yet when it came to protecting its own data, basic AWS configuration discipline failed.
This isn’t even the Commission’s first breach. The pattern is clear: enforcement authority doesn’t translate to operational security. Compliance frameworks don’t prevent human error. And regulations—no matter how strict—can’t protect you from misconfigured cloud accounts.
The Blame Game: AWS vs Customer
AWS was quick to clarify that its “services operated as designed.” Translation: This wasn’t a cloud provider vulnerability. The breach likely originated from the Commission’s identity and access management layer—compromised credentials or overly permissive IAM policies. AWS provides secure infrastructure. Customers must configure it correctly. That’s the shared responsibility model.
The Commission, meanwhile, claimed “internal systems were not affected” while ShinyHunters published a 90GB proof archive on the dark web. Classic breach response playbook: downplay the impact, minimize the scope, deflect blame. Neither AWS nor the Commission wants accountability for a failure that was entirely preventable.
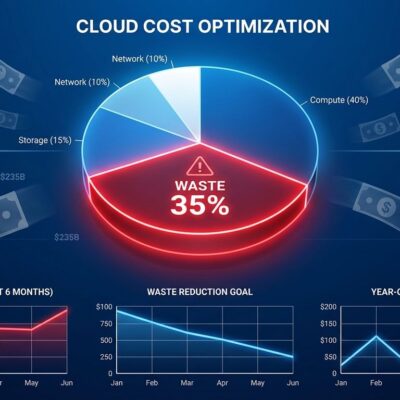
95% of Cloud Failures Are Human Error
The EU Commission breach validates what the industry already knows: 95% of cloud security failures stem from misconfigurations caused by human error, not inherent platform vulnerabilities. Gartner found that 80% of security breaches are caused by misconfiguration-related issues. The average cost of a cloud misconfiguration breach is $4.3 million, up 17% year-over-year. And 70% of cloud environments contain at least one publicly exposed resource.
Cloud providers build secure infrastructure. Customers break it through poor IAM hygiene, weak credential management, and lack of continuous validation. No amount of budget, staff, or regulatory authority changes this reality. The Commission had all three and still failed.
ShinyHunters and the Double Extortion Economy
ShinyHunters operates a straightforward business model: steal data, demand ransom, publish on the dark web if refused, then sell to the highest bidder. Since 2020, the group has breached 300 to 400 companies and leaked personal information from over one billion users. Previous victims include AT&T (110 million customers), Santander (30 million customers), Google, Cisco, and Adidas.
This is double extortion as standard practice. Paying the ransom doesn’t guarantee safety—AT&T paid $370,000 and data still circulated. Organizations need to assume breach and plan incident response, not rely on security theater to prevent attacks that are increasingly inevitable.
What Developers Should Actually Do
The root cause of this breach was almost certainly IAM-related: compromised credentials, excessive permissions, missing MFA, or poor rotation policies. If the EU Commission—with its regulatory authority, enforcement power, and security budget—can’t prevent basic configuration errors, the lesson is clear: cloud security is your job, and manual audits aren’t enough.
Start by auditing all IAM policies and applying least privilege principles. Enforce MFA on every account. Rotate credentials regularly and prefer temporary credentials through IAM roles over long-lived access keys. Enable CloudTrail and AWS Config for continuous monitoring. Adopt Cloud Security Posture Management tools to catch misconfigurations before they become breaches. Automate remediation workflows so gaps close at scale, not through quarterly reviews that miss active threats.
The European Commission breach proves that regulations and enforcement authority don’t protect you from human error. Cloud security requires continuous validation, automated remediation, and clear ownership of the shared responsibility model. Don’t wait for a 350GB breach to take cloud configuration seriously.