Anthropic accidentally published Claude Code’s entire source code today – all 512,000 lines of it – through a source map file included in their npm package. Security researcher Chaofan Shou discovered the leak when the package’s .map file revealed a link to an R2 storage bucket containing 1,900 TypeScript files with the complete unobfuscated codebase. Within hours, the leaked code appeared on GitHub with 1,100+ stars and 1,900+ forks. It’s a packaging mistake that exposed one of the industry’s most popular AI coding tools, and it happened the same day Axios was compromised in a major npm supply chain attack.
The Scope: 512K Lines, Tool Systems, Unreleased Features
The scope of the leak is massive. The exposed codebase includes Claude Code’s tool system (~40 permission-gated tools spanning 29,000 lines), its query engine (46,000 lines handling all LLM API calls), multi-agent orchestration, IDE bridge systems, and even unreleased features like “Kairos” mode. Anthropic quickly pushed an npm update to remove the source maps and deleted earlier versions from the registry, but the damage was done. The GitHub archive is permanent, and developers have already begun dissecting the code.
How It Happened: A Build Configuration Error
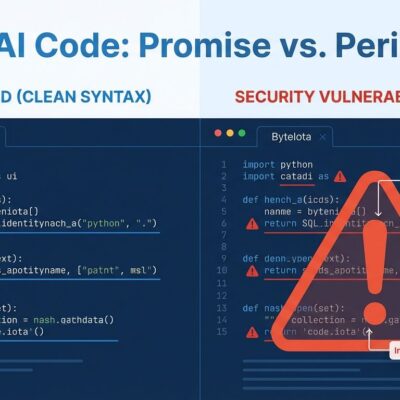
Here’s how it happened: source maps are debugging tools that map minified or bundled code back to the original source. They’re meant for development environments, not production. But a misconfigured .npmignore or files field in package.json failed to exclude .map files from the npm package distribution. As one developer explained on DEV Community, “including one in a production npm publish effectively ships your entire codebase in readable form.” A single build configuration oversight exposed the complete architecture of a tool trusted by thousands of developers.
Same Day as Axios Attack: npm Supply Chain Crisis
The timing is remarkable. The Claude Code leak happened the exact same day that Axios was compromised – one of npm’s most popular packages with 83 million weekly downloads – through a hijacked maintainer account. Attackers deployed a cross-platform Remote Access Trojan (RAT) across macOS, Windows, and Linux. This follows 2025’s record: 454,000 malicious packages published on npm, representing 99% of all open source malware. The average npm project pulls in 79 transitive dependencies, meaning a single compromised package can cascade through millions of applications within hours. While the Claude Code leak wasn’t malicious, it demonstrates exactly how easily npm packages can expose unintended content – source code, credentials, API keys, or internal endpoints.
Lessons for Package Maintainers
If it can happen to Anthropic, it can happen to you. Here’s what package maintainers need to do: use npm pack --dry-run before every publish to see exactly what gets distributed. Explicitly configure .npmignore or the files field in package.json – a whitelist approach is safer than blacklist. Never include .map files unless you have a specific reason. Audit your build artifacts for sensitive files. Implement automated CI/CD checks to catch this before it reaches the registry. Source maps have exposed real secrets before – there’s a documented case of hardcoded Stripe API keys found in production source maps. One configuration error can turn your proprietary codebase public in seconds.
Second Anthropic Leak in Five Days
This is Anthropic’s second major leak in five days. On March 26, a CMS configuration error exposed details about the unreleased “Claude Mythos” model, draft blog posts, and 3,000 unpublished assets. Both incidents stem from configuration errors, not sophisticated attacks. For a company building AI tools that request filesystem, terminal, and codebase access, these operational security lapses raise trust questions. The Hacker News community is divided. Some dismiss it: “The source code of the slot machine is not relevant to the casino manager” – the underlying model matters more than the client code. Others see a red flag: “A company you’re trusting is failing to properly secure its own software.” The pragmatists are studying the leaked code to learn from Claude Code’s architecture.
The Irony of AI Coding Tools
The irony is unavoidable. A tool designed to help engineers write better code and avoid mistakes was brought down by the kind of configuration oversight it’s supposed to prevent. The npm ecosystem moves at incredible speed – packages publish instantly, dependencies update automatically, and vulnerabilities cascade globally within hours. But security practices haven’t kept pace. One misconfigured field in package.json exposed 512,000 lines of code to the world in a matter of hours.
That’s the supply chain reality in 2026. Configuration errors have permanent consequences. Your source code, your secrets, your internal architecture – all one packaging mistake away from becoming public knowledge. The Claude Code leak is a reminder that in the modern software supply chain, every developer is a potential security risk, and every npm publish is a trust transaction.