Anthropic accidentally leaked 500,000 lines of Claude Code‘s internal source code on March 31, 2026, by including a 59.8 MB debugging source map in version 2.1.88 of their npm package. Security researcher Chaofan Shou discovered the leak, which exposed 1,906 proprietary files including 44 unreleased feature flags, anti-distillation mechanisms, and a roadmap for autonomous background agents. This is the SECOND time Anthropic made the exact same mistake—the first leak occurred in February 2025.
The repeated failure isn’t just embarrassing. It undermines Anthropic’s credibility as an “AI safety” company. If they can’t implement basic CI/CD checks to prevent source maps in npm packages—a 10-line bash script—how can developers trust them with sensitive project data?
Claude Code Source Leak: Same Mistake Twice
In February 2025, an early version of Claude Code faced the same source map leak. Anthropic removed the package from npm and deleted the source map. The problem resurfaced in March 2026 despite prior awareness. Making the same mistake twice in 14 months reveals either a botched fix, a reverted patch, or—worst case—no postmortem analysis after the first incident.
Anthropic called it “a release packaging issue caused by human error, not a security breach.” That framing is damage control. Exposing 500,000 lines of proprietary code, internal APIs, security mechanisms, and product roadmap IS a security breach by any standard definition. One mistake is forgivable. Repeating it after awareness indicates broken organizational processes, not isolated human error.
For a company valued at billions that raises money on AI safety credentials, this is inexcusable. The contrast is striking: Anthropic markets itself as the responsible AI company emphasizing safety culture, yet they leaked their flagship product’s source code twice using the same vulnerability. That’s not a technical problem. That’s a culture problem.
What Was Exposed: 44 Unreleased Features
The leak exposed 44 unreleased feature flags and Anthropic’s complete product roadmap. Most significant: KAIROS autonomous mode featuring persistent background agents with /dream memory distillation, GitHub webhooks, and 5-minute cron refreshes. The system includes remote control capabilities (control Claude from phone or another browser) and session review features where Claude analyzes its own previous work.
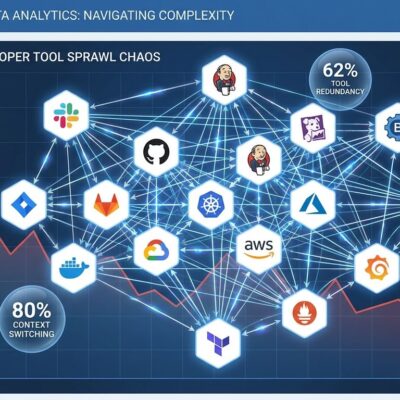
Security analyst Alex Kim nailed the core issue: “The real damage isn’t the code. It’s the feature flags.” Competitors now possess product roadmap details that cannot be unexposed. Cursor, OpenAI, and Replit can copy successful ideas—like KAIROS autonomous mode—and ship them first. They can avoid Anthropic’s mistakes. Anthropic just handed competitors 14 months of R&D insights for free. The competitive damage is permanent. You can’t un-leak a roadmap.
The leak also revealed “undercover mode,” which strips Anthropic internal references from open source contributions to make AI-written code appear human-authored. Community reaction was harsh. Hacker News users argued this violates open source transparency norms where contributors deserve to know if code is AI-generated. Another oddity: frustration detection via regex patterns matching “wtf,” “shit,” and “so frustrating.” Developers called it “peak irony”—an LLM company using grep instead of model inference to detect emotions.
How the npm Source Map Leak Happened
Source maps are JSON files generated during JavaScript/TypeScript compilation that map minified production code back to readable source code. They’re debugging tools meant for internal development only, never public distribution. Anthropic’s source map pointed to a zip archive on their cloud storage containing the full, unobfuscated TypeScript source: 1,906 files, ~512,000 lines.
Chaofan Shou found the leak by examining the npm package contents, discovering the .map file, and following its reference to the cloud storage archive. Within hours, the codebase was mirrored across GitHub and analyzed by thousands of developers. Anthropic removed the package, but too late—the source was already widely distributed.
This is a well-known vulnerability with simple fixes. Most bundlers (webpack, rollup, esbuild) generate source maps by default. You must explicitly disable them for production. The fact Anthropic didn’t implement preventive measures after the FIRST leak is the real story. It suggests organizational dysfunction, not just a one-time mistake.
How to Prevent Source Map Leaks in npm Packages
Preventing source map leaks requires three layers of defense. First, disable source maps in your production build config:
// webpack.config.js - Prevent source map leaks
module.exports = {
mode: 'production',
devtool: false, // Disable source maps in production
optimization: {
minimize: true,
},
};Second, exclude .map files in your .npmignore. Third, add a CI/CD check to fail builds if source maps are detected:
# Pre-publish check - fail build if source maps detected
if find dist -name "*.map" | grep -q .; then
echo "ERROR: Source maps detected - aborting publish"
exit 1
fiThese are standard npm security practices documented by OWASP. Other critical measures: disable lifecycle scripts (the main attack vector for supply chain attacks), implement a 3-day cooldown for new dependencies, use OIDC trusted publishing instead of long-lived tokens, and enable 2FA on npm accounts.
Every developer publishing to npm should verify they’re not leaking source maps. Anthropic’s failure demonstrates that even well-funded companies with prior awareness can repeat the same mistake. The tools and practices exist. Implementation is the only barrier.
Key Takeaways
- Anthropic leaked Claude Code source code TWICE via npm source maps (February 2025 and March 2026). Repeating the same mistake isn’t “human error”—it’s a systemic process failure that raises questions about organizational competence.
- The leak exposed 44 unreleased feature flags including KAIROS autonomous mode, giving competitors 14 months of product roadmap insights. The competitive damage is permanent—code can be refactored, but roadmap reveals cannot be undone.
- Source map leaks are preventable with three simple measures: disable source maps in production configs, exclude .map files in .npmignore, and add CI/CD checks to fail builds if source maps are detected.
- Anthropic’s “not a security breach” framing contradicts reality. Exposing 500,000 lines of proprietary code, internal APIs, and security mechanisms IS a breach by any standard definition. The framing is damage control, not accurate assessment.
- The tension between Anthropic’s AI safety marketing and operational security failures is striking. If they can’t secure their own code after two attempts, trust in their AI safety claims deserves scrutiny.