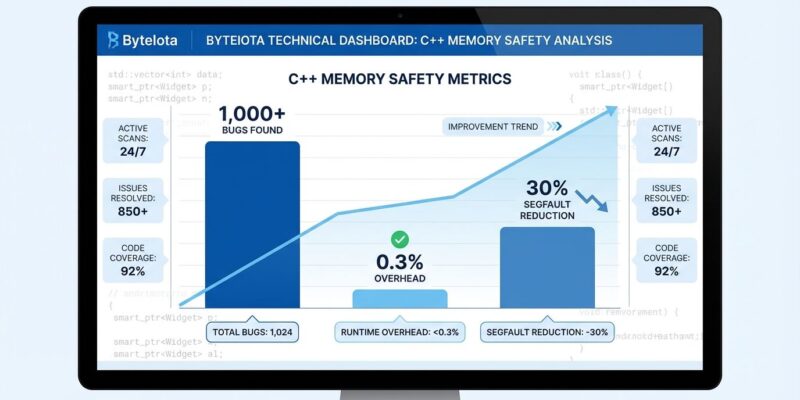
Google deployed hardened libc++ across hundreds of millions of lines of production C++ code—including Search, Gmail, YouTube, and Maps—and uncovered over 1,000 bugs with only 0.3% performance overhead. Some vulnerabilities had lurked undetected for more than a decade. The deployment slashed segfault rates by 30% and is projected to prevent 1,000-2,000 new bugs annually. This proves memory safety can be retrofitted onto massive C++ codebases without rewriting in Rust.
For years, the debate raged: rewrite in Rust or accept the vulnerabilities. Google found the pragmatic answer the industry needs—and the data backs it up.
Google’s C++ Hardening Results: 1,000+ Bugs, 0.3% Overhead
Google’s deployment metrics destroy the myth that runtime safety checks cripple performance. Across critical services—Search, Gmail, YouTube, Maps, and cloud infrastructure—hardened libc++ added an average overhead of just 0.30%. That’s three-tenths of a percent. For context, AddressSanitizer imposes a 2-3x slowdown, making it unusable in production.
The bug discovery numbers tell the real story. Hardening uncovered 1,000+ bugs, including security-critical vulnerabilities. Some had existed for over 10 years, silently waiting to cause memory corruption or exploits. Chandler Carruth, Google’s Distinguished Engineer and C++ Language Lead, noted that hardening “transformed difficult memory corruptions into debuggable errors.” The deployment reduced production segfault rates by 30%—a massive reliability win beyond just security.
Moreover, hardening disrupted an internal red team exercise, proving it prevents real exploits. At Google’s current development pace, it’s projected to stop 1,000-2,000 new bugs yearly. The 0.3% overhead makes this viable for production at any scale.
How C++ Standard Library Hardening Works
Hardening adds runtime bounds checking to standard library operations. When code violates preconditions—like accessing element 10 in a 3-element vector—hardening triggers a contract violation instead of undefined behavior. This catches bugs immediately with debuggable errors rather than letting memory corruption manifest unpredictably.
Consider this example:
std::vector<int> vec = {1, 2, 3};
int x = vec[10]; // Without hardening: undefined behavior (crash, garbage, or exploit)
// With hardening: contract violation (immediate termination)Hardening covers the standard types developers use constantly: std::vector, std::string, std::span, std::string_view, std::optional, std::expected, std::array, and std::mdspan. Each subscript operation, iterator dereference, and optional value access gets checked. When bounds are violated, the program terminates immediately with diagnostic information—no silent corruption, no mysterious crashes miles away from the root cause.
However, hardening doesn’t catch everything. Raw pointer arithmetic, use-after-free, and thread safety issues remain outside its scope. P3471R4, the C++ standard library hardening proposal, addresses spatial memory safety for standard library operations, not complete memory safety. Set expectations accordingly.
Pragmatism vs. “Rewrite in Rust” Purity
This is Google’s answer to regulatory pressure from the White House Office of the National Cyber Director urging memory-safe languages like Rust and Go. While Rust provides compile-time memory safety guarantees, rewriting billions of lines of C++ is economically impractical and introduces massive migration risk.
Google chose a hybrid strategy: harden legacy C++ incrementally, adopt Rust for new critical code where it makes sense. The C++ standards committee rejected the Rust-style approach—Sean Baxter, author of the Safe C++ Extensions proposal, admitted “The Rust safety model is unpopular with the committee.” Instead, P3471R4 (Standard Library Hardening) won approval for C++26, standardizing the runtime checking approach.
Related: TypeScript Leads Promise Index, Rust Leads Reality: 89% vs 43%
The Rust evangelists demand perfection: memory safety or nothing. Google delivered pragmatism: measurable improvement today without betting the company on a complete rewrite. The 1,000+ bugs found, 0.3% overhead, and 30% segfault reduction prove the middle ground works.
How to Enable C++ Hardening in libc++ and MSVC
Hardening isn’t vaporware—it’s shipping today. Google’s libc++ (used by Clang/LLVM) supports it now. Microsoft shipped it in Visual Studio 2022 version 17.14+. The C++26 standard (P3471R4 approved) makes it portable across all compilers. You don’t need to wait for C++26; enable it in C++17, C++20, or C++23 codebases immediately.
Enabling hardening takes one compiler flag:
# libc++ (Clang)
clang++ -std=c++20 -D_LIBCPP_HARDENING_MODE=hardened mycode.cpp
# MSVC (Visual Studio 2022 17.14+)
cl /std:c++20 /D_MSVC_STL_HARDENING=1 mycode.cppStart by enabling hardening in CI/CD and test environments. Google spent over a year in testing before production rollout, uncovering hundreds of bugs early. When tests fail due to contract violations, fix the bugs—they’re real issues that previously caused undefined behavior. Monitor performance overhead in your specific workload (Google saw 0.30% on average, but measure for yourself). Gradually roll out to production services after thorough testing.
Remember the limitations. Hardening checks standard library bounds violations—not raw pointer misuse, not lifetime bugs like use-after-free, not thread safety issues. It’s a significant improvement, not a complete solution. Raw pointers and manual memory management remain dangerous. Use standard library types (std::vector, std::span, std::unique_ptr) over raw arrays and pointers whenever possible to maximize hardening coverage.
Key Takeaways
- Google proved memory safety retrofitting works at massive scale: 1,000+ bugs found with 0.3% overhead across Search, Gmail, YouTube, and Maps.
- Hardening addresses the “rewrite in Rust” impasse by providing a pragmatic path for existing C++ codebases—improve incrementally rather than betting on complete rewrites.
- It’s production-ready now: libc++ (Clang), MSVC (Visual Studio 2022 17.14+), and standardized in C++26 (P3471R4 approved).
- Enable in CI/CD first, test thoroughly (Google took 1+ year), then gradually roll to production while monitoring overhead.
- Set realistic expectations: hardening catches standard library bounds violations, not raw pointer misuse, lifetime bugs, or thread safety issues—it’s spatial safety for standard types, not complete memory safety.
Google chose pragmatism over purity, and the data validates the approach. For the billions of lines of C++ that will exist for decades, hardening offers measurable safety improvements without the cost and risk of wholesale rewrites.