North Korea just weaponized the JavaScript ecosystem. On March 31, 2026, threat actors compromised Axios—the most-downloaded npm package for HTTP requests with 100+ million weekly downloads—and deployed cross-platform malware to thousands of developers during a 3-hour window. Google attributes the attack to UNC1069, a North Korean group that stole $2.02 billion in cryptocurrency in 2025 alone. This is how they did it, and what every JavaScript developer needs to do now.
The Attack Chain: 39 Minutes to Compromise
The attack was surgical. Attackers compromised Jason Saayman’s maintainer account, changed the email to ifstap@proton.me, obtained a long-lived npm token, and published two malicious versions within 39 minutes: axios@1.14.1 at 00:21 UTC and axios@0.30.4 at 01:00 UTC on March 31.
Neither version touched Axios’s code. Both added a single dependency: plain-crypto-js@4.2.1, which existed solely to execute a postinstall hook—npm’s automatic execution mechanism. No warnings. No consent. When developers ran npm install, the hook fired, downloading platform-specific malware from sfrclak[.]com:8000. Windows got PowerShell malware, macOS received a C++ Mach-O binary, Linux systems got Python backdoors. All delivered WAVESHAPER.V2.
Elastic Security Labs detected the compromise via automated monitoring—not npm itself. By removal at 03:29 UTC, roughly 3% of the Axios userbase had downloaded malicious versions. With Axios in 80% of cloud environments, the blast radius is enormous.
WAVESHAPER.V2: Nation-State RAT
WAVESHAPER.V2 is nation-state tooling: a cross-platform Remote Access Trojan with full system access. It beacons to C2 servers every 60 seconds and supports four commands: kill (terminate), rundir (enumerate files), runscript (execute OS-specific commands), and peinject (run arbitrary binaries via in-memory injection on Windows).
The malware harvests system details—hostname, username, OS version, running processes—then waits for commands. On Windows, it executes in-memory (no files dropped), making detection harder. If you installed Axios during that 3-hour window, this landed on your system. It’s designed to steal cryptocurrency wallets, credentials, and API keys—exactly what North Korea uses to fund operations by draining DeFi platforms.
UNC1069: $2B in Crypto Theft, Now Targeting Developers
Google attributed the attack to UNC1069, a North Korean threat actor active since 2018 (also tracked as CryptoCore, MASAN). The group stole $200 million from crypto exchanges between 2018-2020, then shifted to Web3: CEXs, DeFi platforms, and VC funds.
In 2025, North Korean groups stole a record $2.02 billion in cryptocurrency—60% of all global crypto thefts. UNC1069 now uses AI-generated deepfake videos in social engineering, posing as investors via compromised Telegram accounts. This npm attack fits their playbook: target high-value software used by crypto developers, deploy sophisticated malware, exfiltrate credentials. JavaScript developers are now combatants in a geopolitical conflict they never signed up for.
npm’s Security Model Is Broken
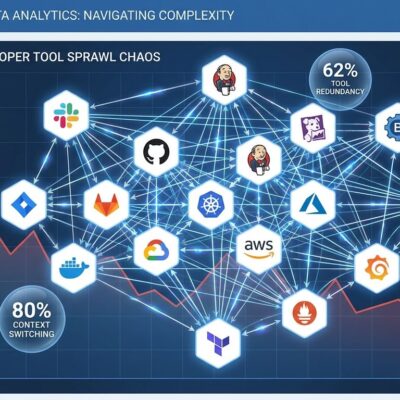
Postinstall hooks execute automatically with zero user consent. A single compromised maintainer account weaponizes the entire ecosystem in under an hour. npm has no mandatory 2FA for high-impact packages. Long-lived tokens allow persistent access even after password changes.
npm detected nothing—third-party vendors caught it. The malicious versions were removed, but 3% of Axios users downloaded compromised code. Lockfiles didn’t help. npm audit didn’t help. The attack succeeded because npm treats untrusted code as trusted by default.
In September 2025, 200+ npm packages were compromised. Axios is just the highest-impact example of a systemic problem. Even pnpm v10 now disables postinstall scripts by default, acknowledging what npm won’t: automatic code execution from untrusted sources is too dangerous.
What You Need to Do Now
Check dependencies immediately. Run npm list axios to see your version. Search for the malicious dependency: find node_modules -name "plain-crypto-js". If found, assume full compromise and rotate all credentials—API keys, database passwords, cloud tokens, wallet keys.
If you installed Axios during March 31, 00:21-03:29 UTC, block C2 domain sfrclak[.]com and IP 142.11.206[.]73 in your firewall. Scan processes for WAVESHAPER.V2 signatures. Check logs for unusual outbound connections during npm install.
Pin Axios to the last safe version: axios@1.14.0 in package.json. Use lockfiles and run npm ci in CI/CD. But understand: lockfiles don’t protect against compromised registry packages, only version drift.
For long-term defense, disable postinstall hooks in CI/CD: npm install --ignore-scripts. Maintain an allowlist for trusted packages requiring scripts. Implement dependency scanning with Snyk, Socket.dev, or npm audit. Monitor outbound connections during builds. Adopt SBOM practices to track dependencies.
npm isn’t going to fix this. No mandatory 2FA for high-impact packages. No postinstall sandboxing. npm didn’t detect this attack—security vendors did. Supply chain security is your problem now. Axios won’t be the last high-impact package compromised.