Motorola announced a partnership with the GrapheneOS Foundation at Mobile World Congress on March 1-3, making it the first non-Google manufacturer to support the privacy-focused Android OS. The breakthrough centers on bootloader relocking—Motorola’s engineering teams enabled verified boot with relockable bootloaders on select flagship hardware, a technical capability previously exclusive to Google Pixels. This ends GrapheneOS’s decade-long Pixel exclusivity and breaks Google’s de facto monopoly on “secure + open” Android devices. First Motorola-GrapheneOS devices launch in 2027 targeting flagship models like the razr fold, razr ultra, and Signature series.
The Bootloader Breakthrough: Security Without Compromise
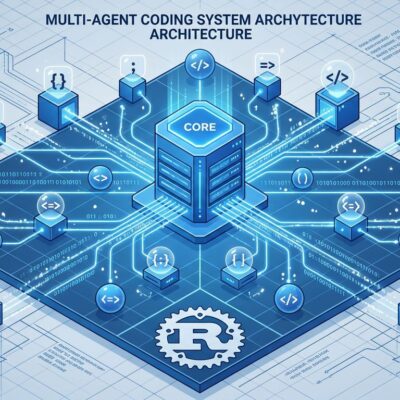
Bootloader relocking enables verified boot with custom operating systems—a critical security feature that ensures only cryptographically signed, trusted software runs on the device. Unlocked bootloaders disable verified boot, meaning anyone with physical access can flash malicious firmware. Relocked bootloaders restore the security chain while allowing custom OSes like GrapheneOS.
The technical flow works like this: device boots from hardware root of trust containing cryptographic keys, bootloader verifies OS signatures, system partitions are checked against cryptographic hashes during every file read, and rollback protection prevents downgrading to vulnerable versions. Most custom Android ROMs (LineageOS, CalyxOS) require keeping the bootloader unlocked, which sacrifices security for customization.
Until now, only Google Pixels allowed users to unlock, install GrapheneOS, then relock with custom signing keys stored in an “avb_custom_key” virtual partition. Motorola engineered the same capability—custom root of trust that allows verified boot with GrapheneOS. Privacy users no longer have to choose between security (verified boot) and hardware freedom (non-Google OEM).
GrapheneOS: Android Privacy’s Gold Standard
GrapheneOS is a hardened Android fork that strips all Google tracking by default and implements enterprise-grade security. Key features include a hardened memory allocator that defends against heap corruption with zero-on-free and write-after-free detection, sandboxed Google Play that runs as an unprivileged app with no system access (maintaining app compatibility without granting Google privileges), and per-app network permission toggles that reliably block network access without relying on VPNs.
The OS also includes duress PIN for irreversible wipe if coerced and LTE-only mode that disables 2G/3G (IMSI catcher risk) and 5G (bleeding-edge attack surface). It’s been Pixel-exclusive since 2014 because only Pixels met strict requirements: unlockable + relockable bootloader, hardware security features like secure elements and memory tagging, and 7-year security update commitment.
GrapheneOS philosophy is deliberately narrow: “Broad device support is counter to the aims of the project.” The project prioritizes deep security integration with specific hardware over supporting many devices. Motorola’s bootloader breakthrough validates this approach—proving that other OEMs can meet GrapheneOS standards if they invest the engineering effort.
Google’s “Open Android” Paradox Challenged
Android claims to be an open platform, but until now, only Google Pixel devices supported secure custom ROMs with verified boot intact. This created an absurd paradox: to escape Google’s surveillance ecosystem, privacy-conscious users had to buy Google hardware. The irony wasn’t lost on the developer community.
The Hacker News discussion (674 points, 198 comments) largely celebrated the end of Pixel lock-in. One commenter captured the geopolitical angle: “The rest of the world yearns for a phone that is cheap, has many years of updates, and not directly subject to US government control. Motorola on GrapheneOS can run away with this.”
The partnership also validates GrapheneOS for enterprise BYOD scenarios where IT departments want de-Googled devices but company policy prohibits Pixel procurement. Android Enterprise’s Device Trust API uses 20+ trust signals to validate security posture without invasive MDM—GrapheneOS on Motorola fits this model perfectly. Motorola’s ThinkShield integration (Lenovo’s enterprise security platform) signals they’re targeting corporate buyers, not just enthusiasts.
Related: TikTok Rejects End-to-End Encryption: Privacy vs Safety
The Catch: Motorola’s Track Record and Lenovo’s Shadow
Despite enthusiasm, skepticism is warranted. Motorola delayed the launch from 2026 to 2027 because hardware requirements weren’t fully met initially—a red flag about execution capability. Motorola (Lenovo-owned since 2014) has a poor track record for long-term software updates, historically providing 2-3 years of support compared to GrapheneOS’s 5-7 year requirement and Pixel 8’s 7-year guarantee.
Lenovo’s Chinese ownership raises credibility questions for some users. As one Hacker News commenter put it: “Given the CCP’s privacy record, the idea of a privacy product controlled by Lenovo is somewhat questionable.” While GrapheneOS’s open-source nature and reproducible builds reduce vendor trust requirements, the optics matter for enterprise buyers.
App compatibility remains uncertain. Even with a relocked bootloader, banking apps may detect the custom OS via Play Integrity checks and refuse to run. There’s no universal solution—compatibility is app-by-app. For users who need perfect app compatibility, GrapheneOS isn’t the answer regardless of hardware.
Key Takeaways
- Motorola breaks Google Pixel’s monopoly on secure Android custom ROMs with bootloader relocking breakthrough announced at MWC 2026, enabling verified boot with GrapheneOS while maintaining enterprise-grade security.
- Bootloader relocking matters: unlocked bootloaders disable verified boot and expose devices to physical attacks, while relocked bootloaders with custom root of trust allow GrapheneOS to maintain the security chain—previously only Pixels supported this.
- GrapheneOS is the gold standard for Android privacy with hardened memory allocator, sandboxed Google Play, and per-app network controls, but has been Pixel-exclusive for 12 years because only Pixels met strict hardware security and update requirements.
- First Motorola-GrapheneOS devices launch in 2027 targeting flagship hardware (razr fold, razr ultra, Signature series), validating GrapheneOS for enterprise BYOD environments and international markets where Google services are restricted.
- Skepticism warranted: Motorola’s poor update track record (2-3 years vs Pixel’s 7), Lenovo’s Chinese ownership, and delayed 2027 timeline (initially planned 2026) raise questions about long-term commitment and execution.