The Trivy vulnerability scanner—one of the most widely-used security tools in CI/CD pipelines—was compromised for the second time in 30 days. On March 19, 2026, attackers calling themselves “TeamPCP” force-pushed malicious code into 75 of 76 version tags in the aquasecurity/trivy-action GitHub Action, injecting credential-stealing malware that silently harvested SSH keys, cloud credentials, and secrets from thousands of automated workflows. The security scanner had become a security threat.
How the Attack Worked: Git Tag Manipulation
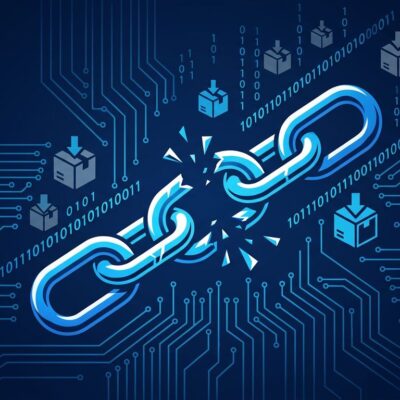
Attackers exploited a fundamental weakness in GitHub Actions: Git tags are mutable. By force-pushing 75 version tags to point to malicious commits, they bypassed GitHub’s release system entirely. When workflows referenced aquasecurity/trivy-action@v0.28.0 (a tag, not a commit SHA), they automatically pulled the attacker’s code.
The malicious payload ran in five stages: discovering GitHub Actions runner processes, scraping process memory and filesystems for credentials, encrypting stolen data with AES-256 and RSA-4096, exfiltrating to a typosquatted domain (scan.aquasecurtiy[.]org), then cleaning up and running the legitimate Trivy scan. The attack window lasted approximately 12 hours (March 19 17:43 UTC to March 20 05:40 UTC), affecting 45+ repositories with over 100 stars.
The malicious entrypoint.sh ballooned to 17,592 bytes compared to the legitimate 2,855 bytes, yet most monitoring systems missed it. The malware executed credential theft before the real security scan ran, making detection nearly impossible through standard logging.
The Incident Response Failure: Fool Me Twice
This wasn’t Trivy’s first compromise. In late February 2026, an autonomous AI agent called “hackerbot-claw” exploited a workflow to steal a Personal Access Token. Aqua Security responded by rotating credentials—but the rotation wasn’t atomic. As the company admitted: “We rotated secrets and tokens, but the process wasn’t atomic, and attackers may have been privy to refreshed tokens.”
That multi-day rotation window gave attackers exactly what they needed: access to the newly rotated credentials. When all old credentials aren’t revoked simultaneously, attackers can maintain persistence by exfiltrating fresh tokens during the transition. The second attack, just 30 days later, exploited this textbook incident response failure.
What Was Stolen: The Credential Harvest
Self-hosted GitHub Actions runners faced the broadest targeting. The malware scraped filesystems for SSH private keys, cloud credentials (AWS, GCP, Azure config files), Kubernetes tokens, Docker registry credentials, database connection strings, CI/CD secrets, Terraform state files, TLS certificates, and even cryptocurrency wallet keys.
The backup exfiltration method was particularly clever. If the primary command-and-control server failed, the malware created public repositories named tpcp-docs, generated timestamped releases, and uploaded encrypted payloads as release assets. This used GitHub’s own infrastructure for exfiltration—harder to block than external C2 traffic and blending into normal development activity.
Organizations should immediately search for tpcp-docs repositories in their GitHub organizations. Presence indicates successful exfiltration.
What Developers Must Do Now
Three immediate actions are required. First, stop using trivy-action by tag reference. Only pin to commit SHA 57a97c7e7821a5776cebc9bb87c984fa69cba8f1 (v0.35.0) or later safe versions. Second, rotate all secrets that were accessible to CI/CD pipelines during March 19-20, 2026. Third, search for tpcp-docs repositories.
Vulnerable workflow (DO NOT USE):
uses: aquasecurity/trivy-action@v0.28.0 # ❌ Tag reference is vulnerableSecure workflow (REQUIRED):
uses: aquasecurity/trivy-action@57a97c7e7821a5776cebc9bb87c984fa69cba8f1 # ✓ SHA pinned (v0.35.0)Tag-based pinning is fundamentally insecure. Tags can be force-pushed at any time, instantly compromising every workflow that references them. Only commit SHAs are immutable. Organizations should audit every GitHub Actions workflow for tag references and enforce SHA pinning via GitHub’s allowed actions policy.
Related: GitHub’s Reliability Crisis: 8 Outages in 2 Months (2026)
Supply Chain Security in 2026: A Disturbing Trend
Trivy is part of a broader pattern. Supply chain attacks targeting GitHub Actions increased dramatically in 2025-2026, with autonomous AI agents, self-propagating worms, and sophisticated tag manipulation becoming commonplace. The first Trivy attack used an autonomous agent that could read workflow YAML, identify misconfigurations, and exfiltrate secrets—all without human intervention.
The irony cuts deep: a security tool became a security threat. This exposes a systemic vulnerability not just in Trivy, but in how we trust dependencies. GitHub Actions, npm, PyPI, and other package ecosystems all face the same mutable reference problem. Individual vigilance (SHA pinning, credential rotation) must be supplemented by platform-level solutions like tag immutability and built-in verification mechanisms.
Key Takeaways
- Trivy was compromised twice in 30 days because non-atomic credential rotation gave attackers persistent access to newly rotated secrets
- Git tag mutability is a systemic vulnerability: 75 version tags were force-pushed to inject malware into thousands of CI/CD pipelines automatically
- Immediately rotate all CI/CD secrets from March 19-20, 2026, and search GitHub organizations for
tpcp-docsrepositories (indicates successful data exfiltration) - Convert all GitHub Actions workflows from tag pinning to SHA pinning—only commit SHAs are immutable and safe from force-push attacks
- Enforce SHA pinning organization-wide via GitHub’s allowed actions policy to prevent this attack vector across your entire supply chain
Sources: CrowdStrike technical analysis, GitHub Security Advisory, Aqua Security incident response, Socket.dev threat analysis